We are already on the verge of throwing away basic auth and EWS (Exchange Web Services). There are tons of applications that retrieve attachments and messages using basic auth or Exchange Web Services. So they need to start using Oauth with Microsoft Graph to retrieve messages and attachments so that legacy dependencies can be safely removed to secure the environment further. In this article, I have explained how an application can access a specific service account only to retrieve its attachments and messages and not the whole environment. if the application needs to read mailboxes across the environment then you need to use New-ApplicationAccessPolicy to scope the permission to a particular set of users which I covered in the end. What we are looking for here is a basic application that needs to retrieve its attachments from its mailbox only and not from the whole environment.
Service Account to retrieve messages and attachments from a specific Microsoft 365 mailbox using an API (Microsoft Graph) would be a safe way to say.
- Creating an Azure AD application
- Create a test account with a mailbox and add some attachments
- Use PostMan to retrieve the same using Microsoft Graph
let’s see how to do it. Login to https://aad.portal.azure.com/
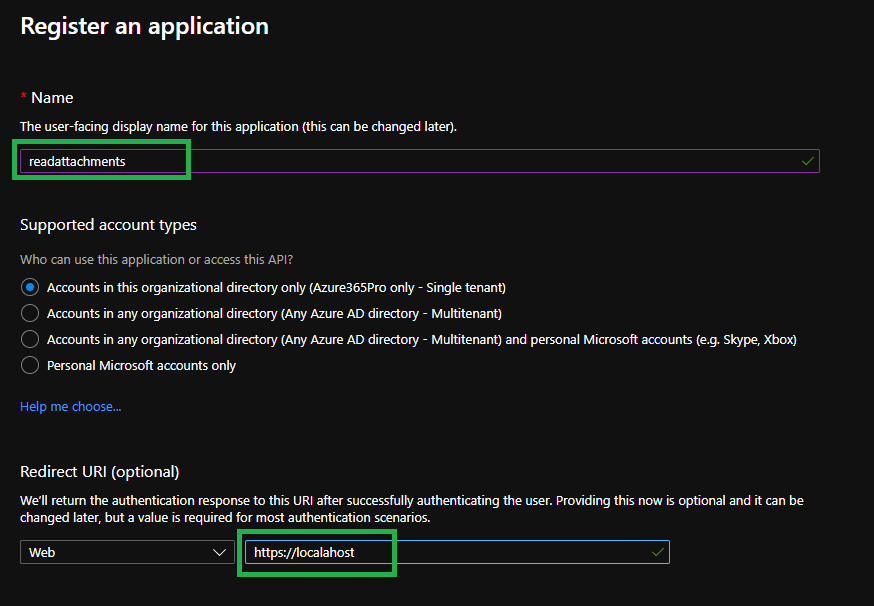
Azure Active Directory – App Registrations – New Registration
readattachments app – register the application
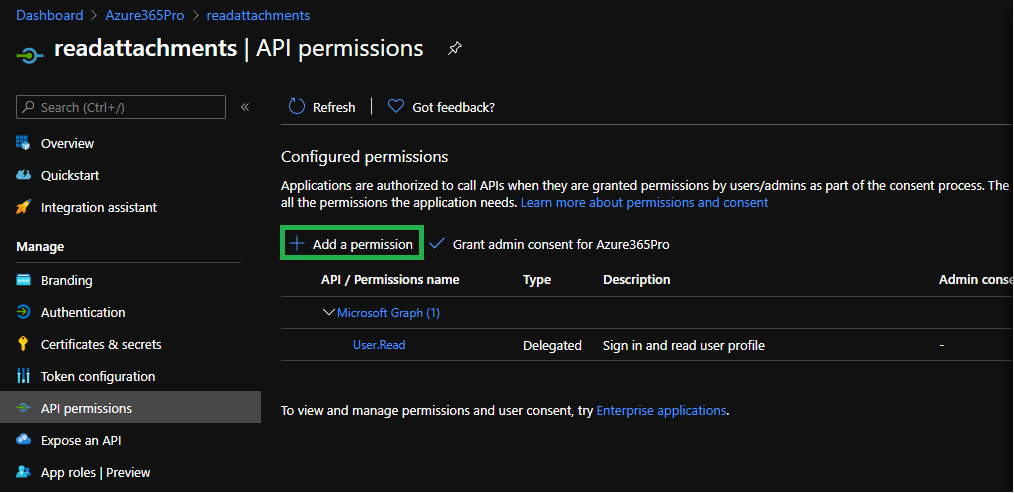
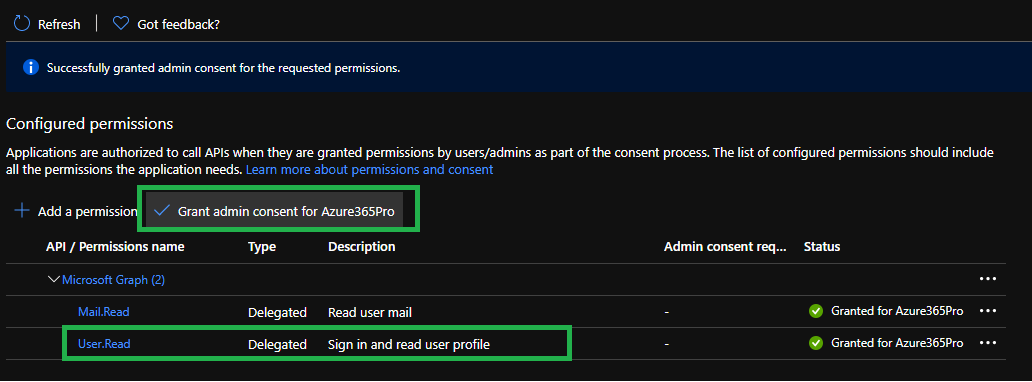
Click on API permissions – Add a Permission
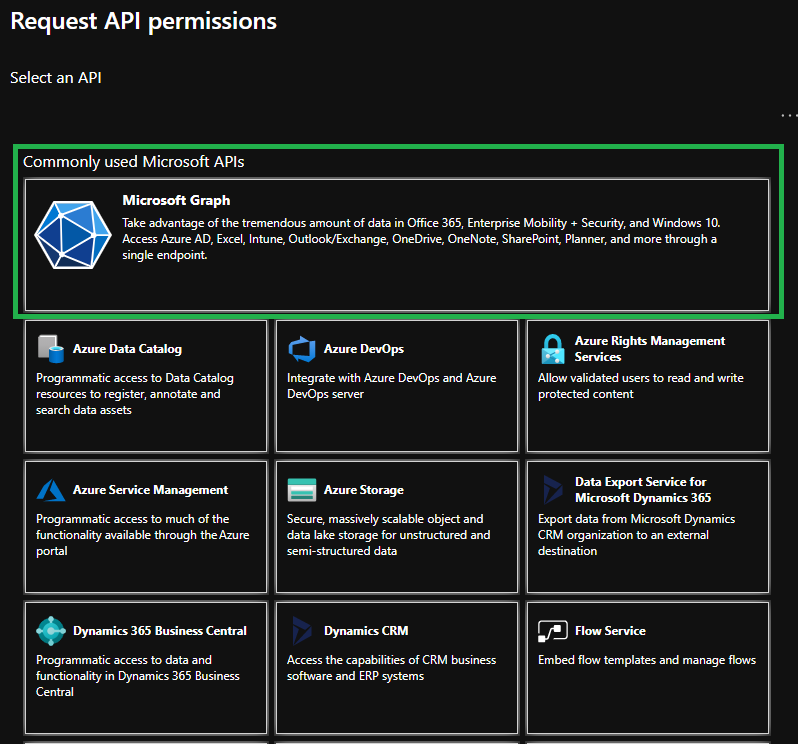
Choose Microsoft Graph
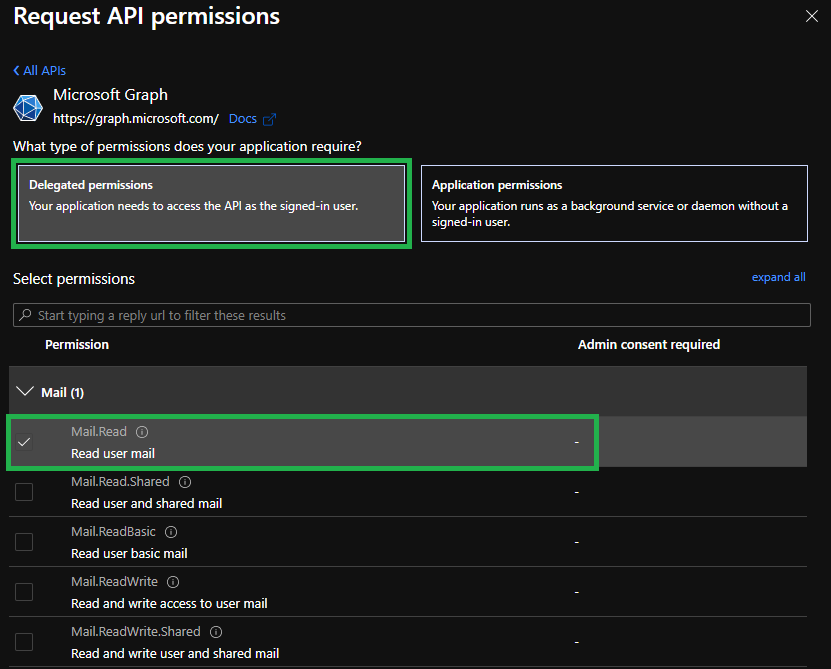
Choose Delegated Permissions – Mail.Read (Allows the app to read the signed-in user’s mailbox.)
Note :
Delegated Permission Used for – Sign-in Users
Application Permission Used for – Applications
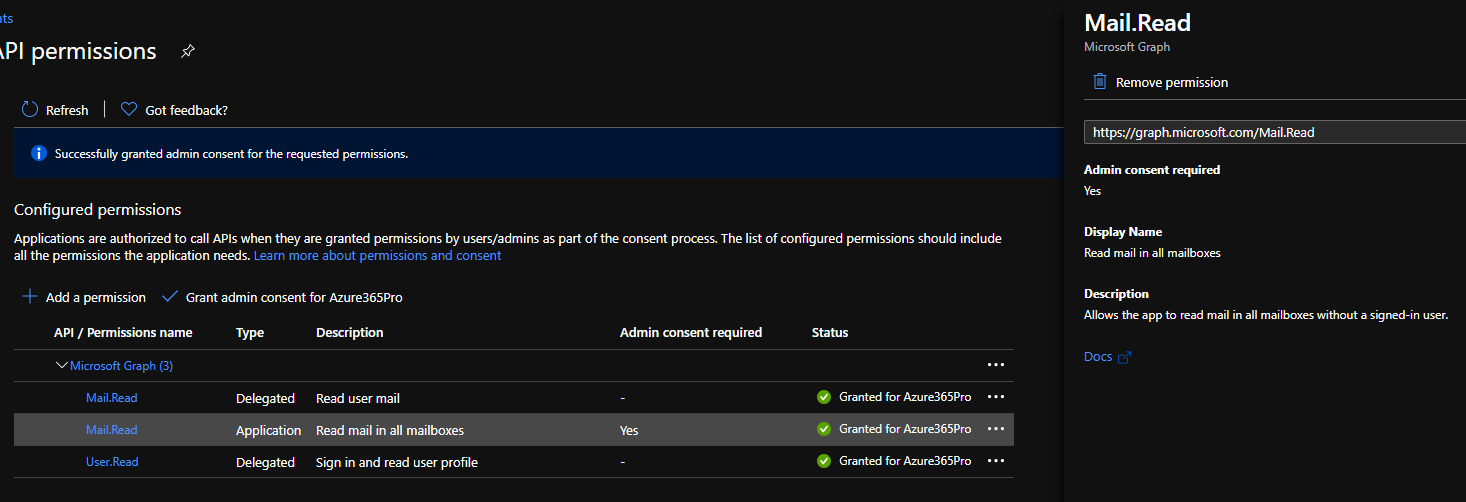
Grant Admin Consent – You can see the green mark “Granted for Azure365pro”
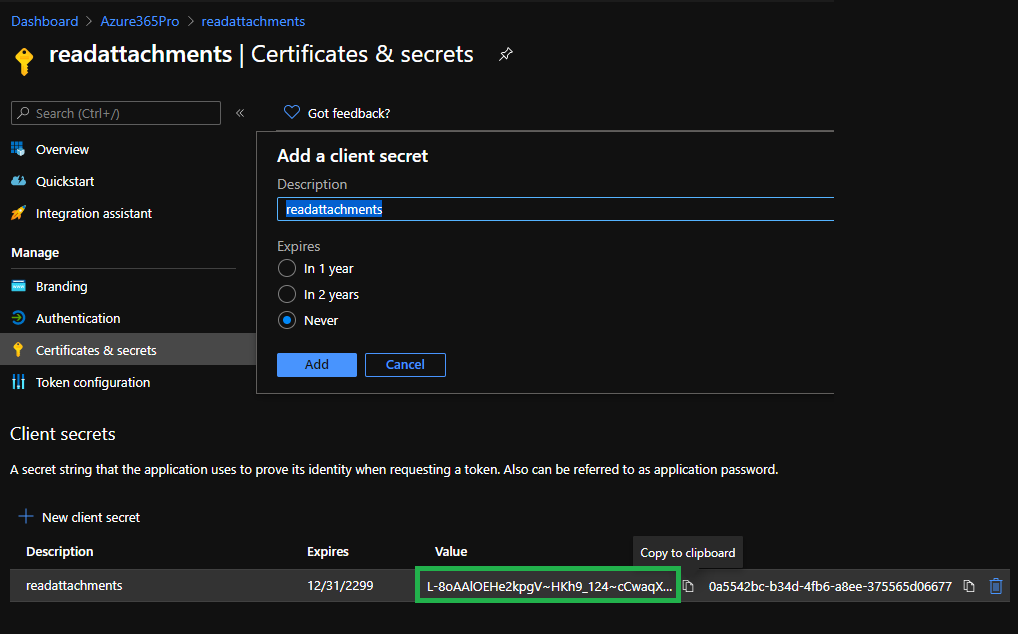
Certificates & Secrets – Client Secrets – New Client Secret
Copy your own Secret L-8oAAlOEHe2kpgV~HKh9_124~cCwaqX7u
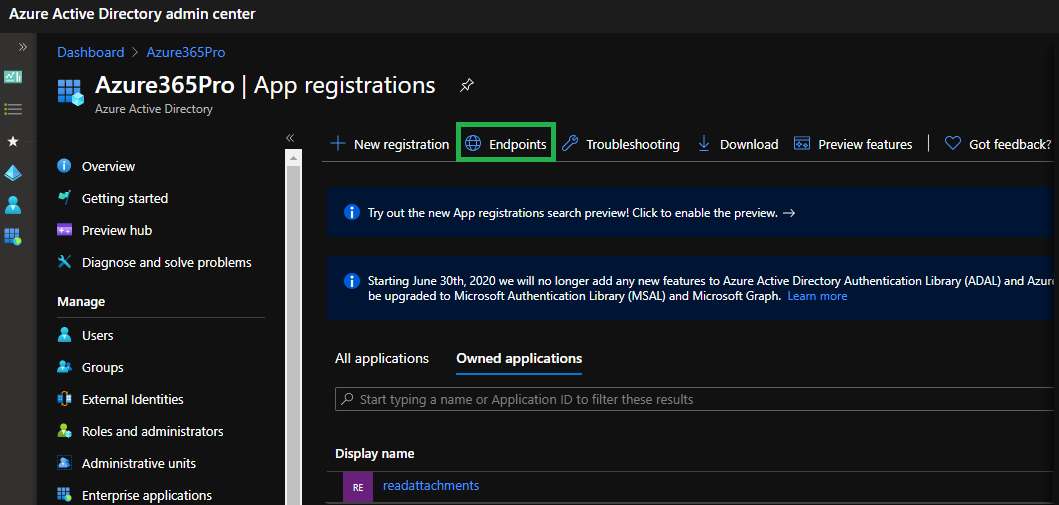
Click on endpoints
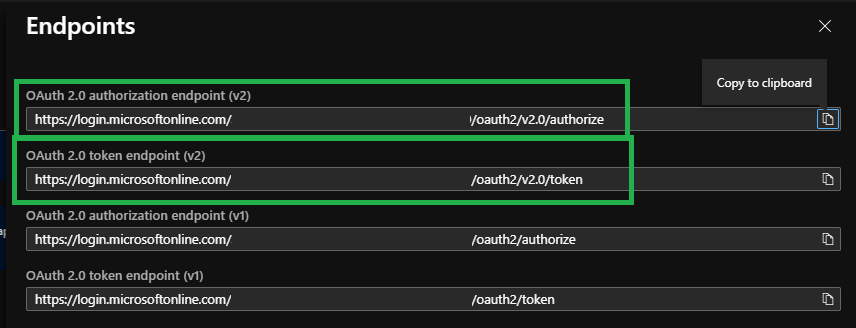
Auth URL = OAuth 2.0 authorization endpoint (v2) = https://login.microsoftonline.com/2549c50e-e478-0000-82cf-fa4efb5d000/oauth2/v2.0/authorize
Access Token URL = OAuth 2.0 token endpoint (v2) = https://login.microsoftonline.com/2549c50e-e478-0000-82cf-fa4efb5d0000/oauth2/v2.0/token
Copy Both URLs
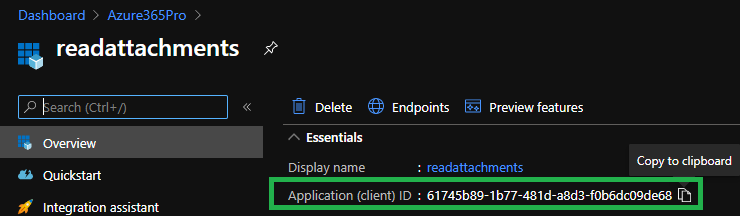
Application (Client) ID
Created a Service mailbox that will receive the attachments
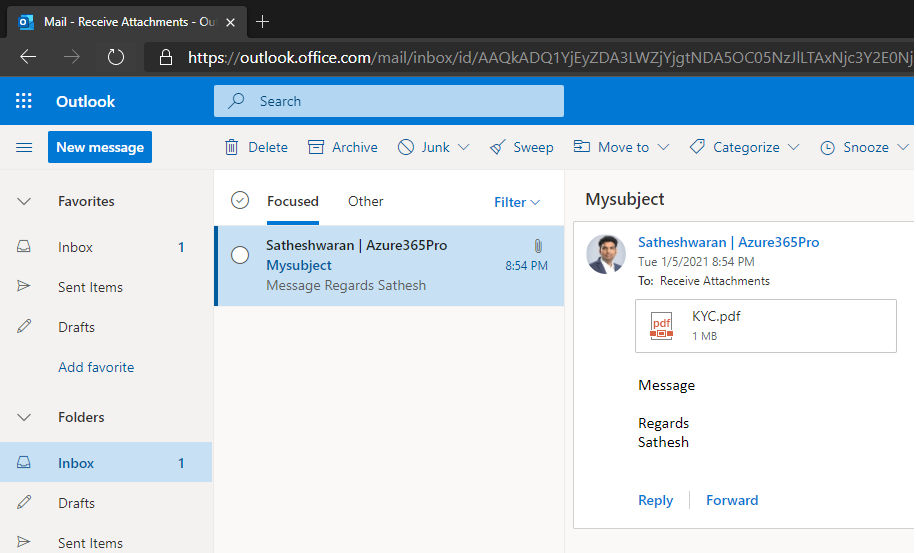
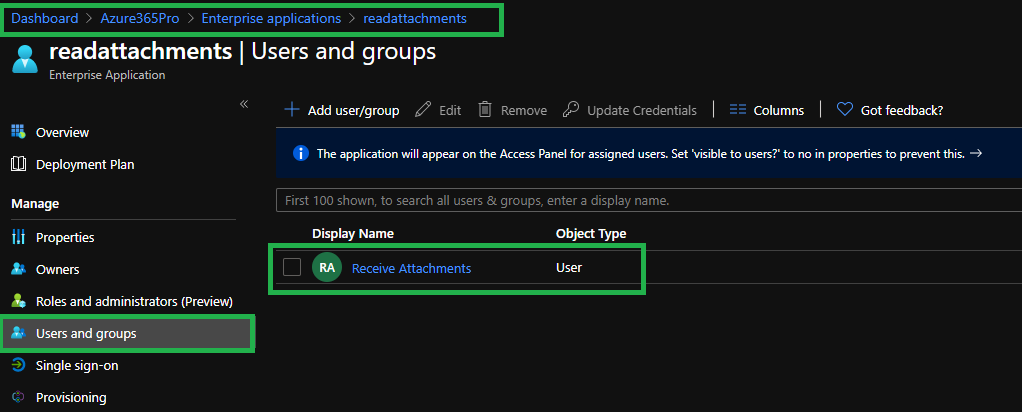
Assign the service account to access the application
Postman is your best friend when it comes to testing Oauth
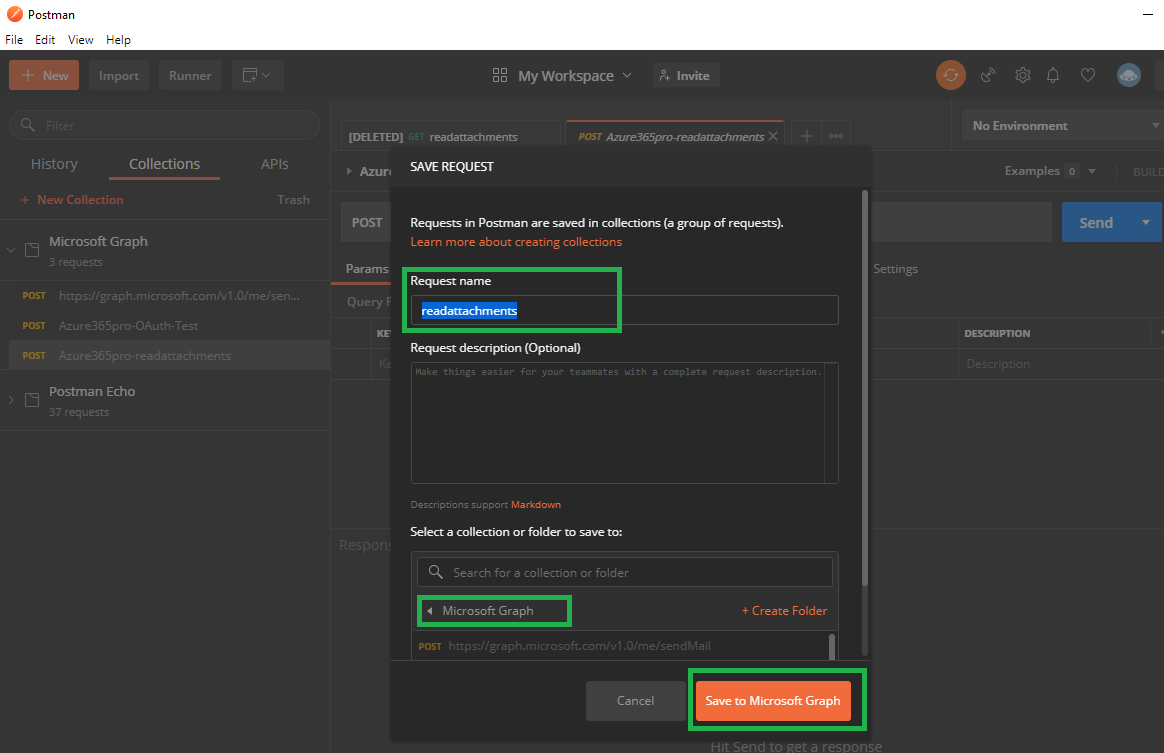
New – Request
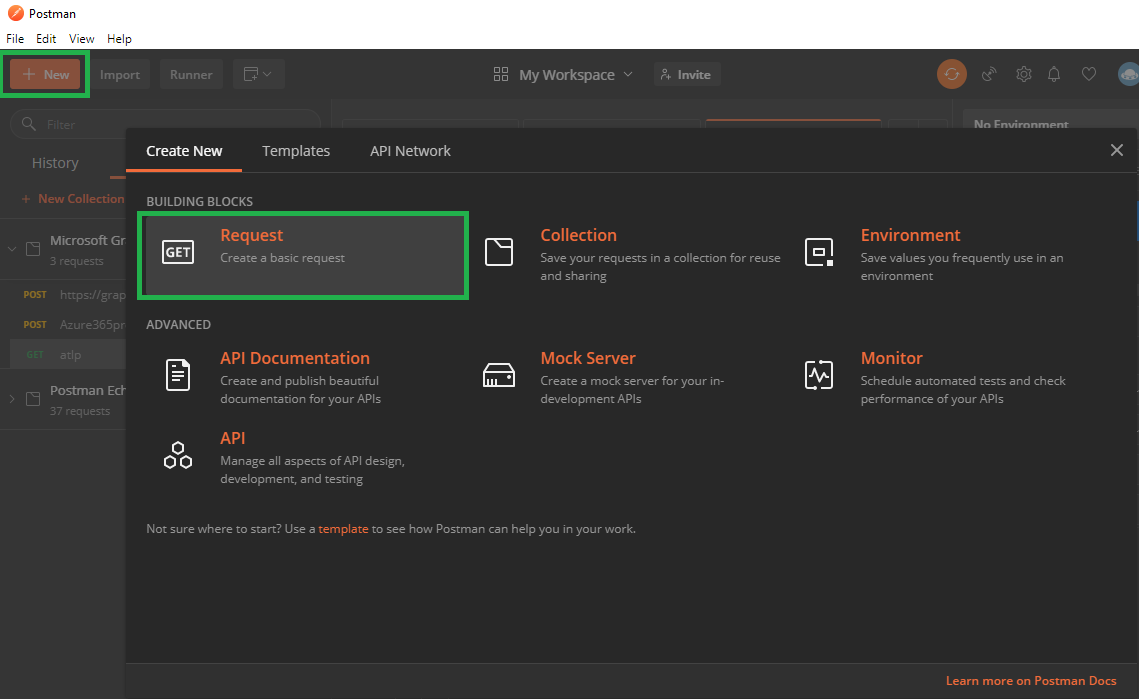
create a request name read the attachments
Request Token – Once you filled all the below information
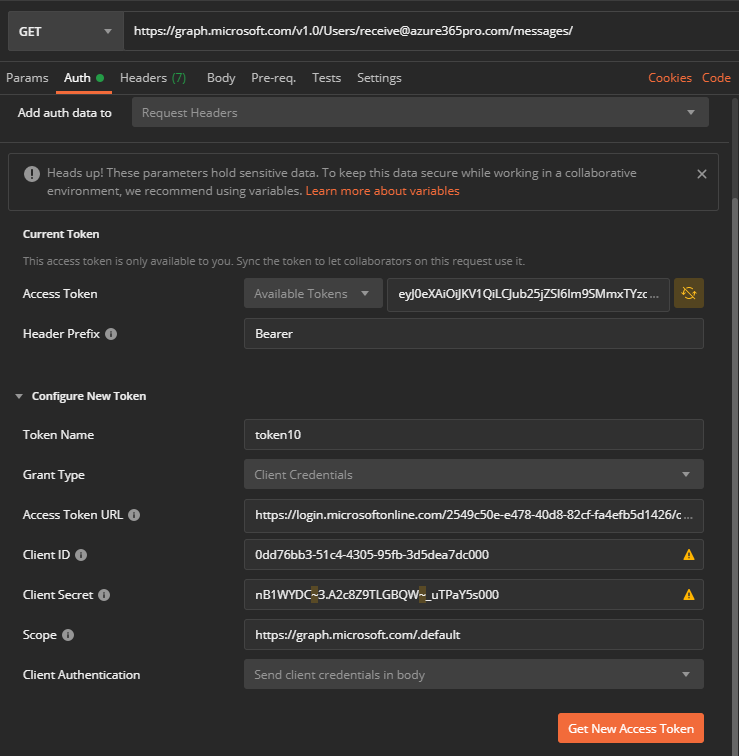
Now you have your Token Name = Friendly Name Grant Type = Authorization Code Callback URL = https://localhost Auth URL = OAuth 2.0 authorization endpoint (v2) - Use it from your tenant - https://login.microsoftonline.com/2549c50e-e478-0000-82cf-fa4efb5d1426/oauth2/v2.0/authorize Access Token URL = OAuth 2.0 token endpoint (v2) - Use it from your tenant - https://login.microsoftonline.com/2549c50e-e478-0000-82cf-fa4efb5d1426/oauth2/v2.0/token Client ID = (Get it from the Overview Tab like below) - Use it from your tenant - 61745b89-1b77-481d-a8d3-f0b6dc09de68 Client Secret = (Get it from Certificates and Secrets Tab like above) - Use it from your tenant - L-8oAAlOEHe2kpgV~HKh9_124~cCwaqX7u Scope = https://graph.microsoft.com/.default State = State Client Authentication = Send Client Credentials in body
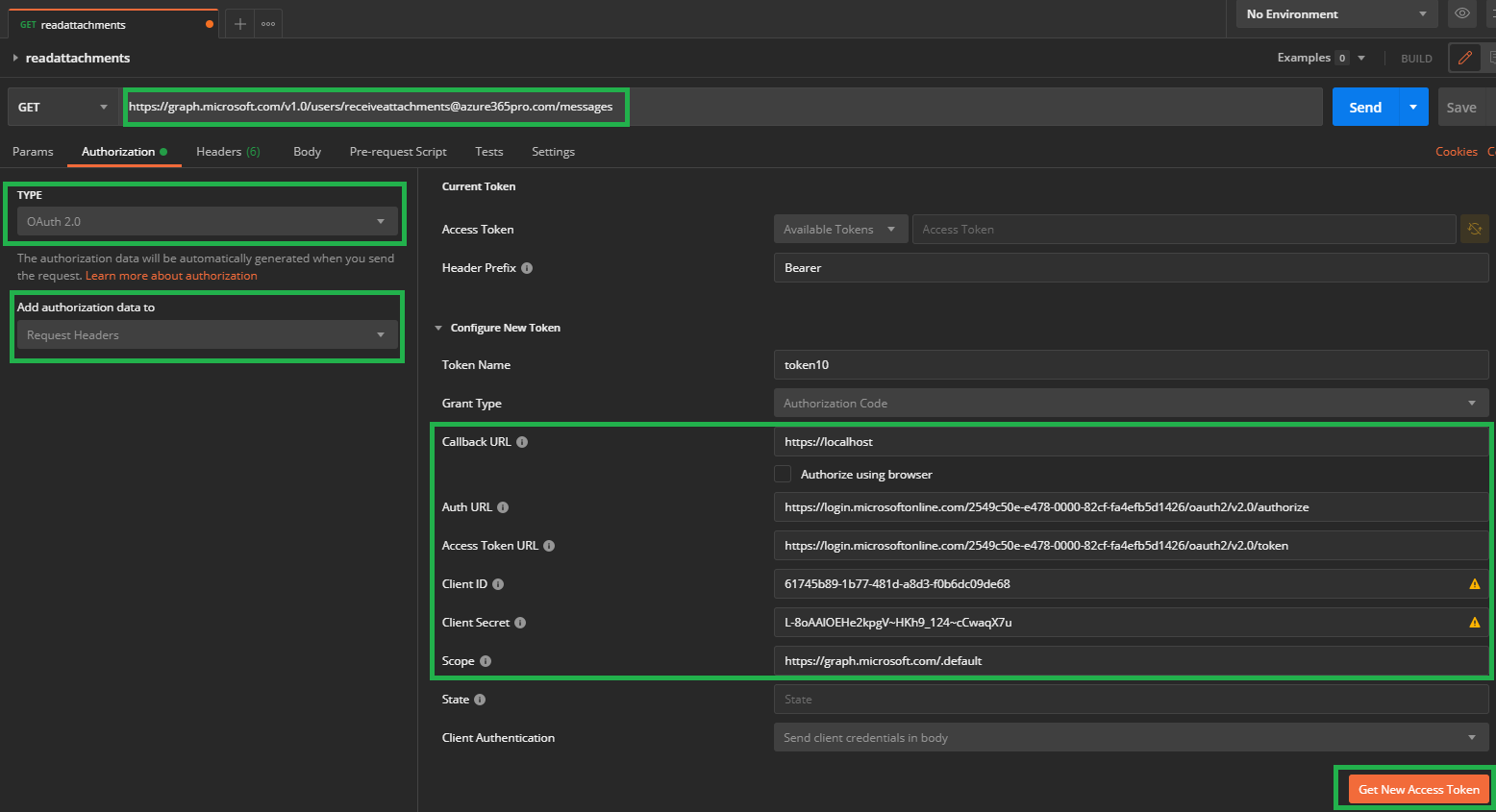
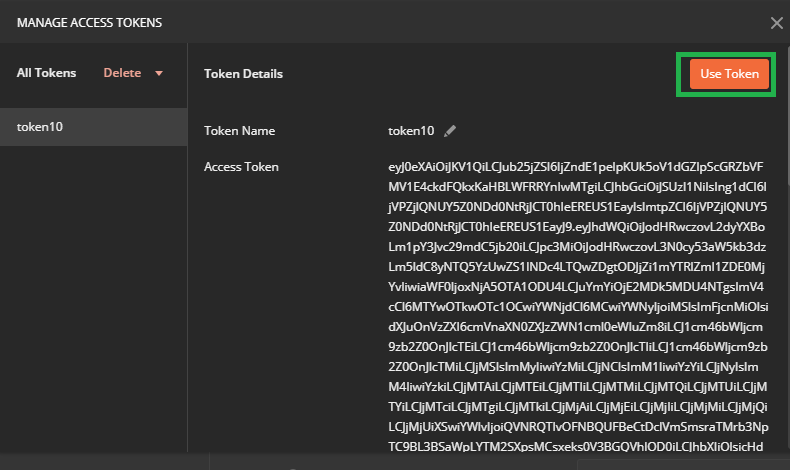
Get new access token – used my service account credential to enter – received the token
Choose use token
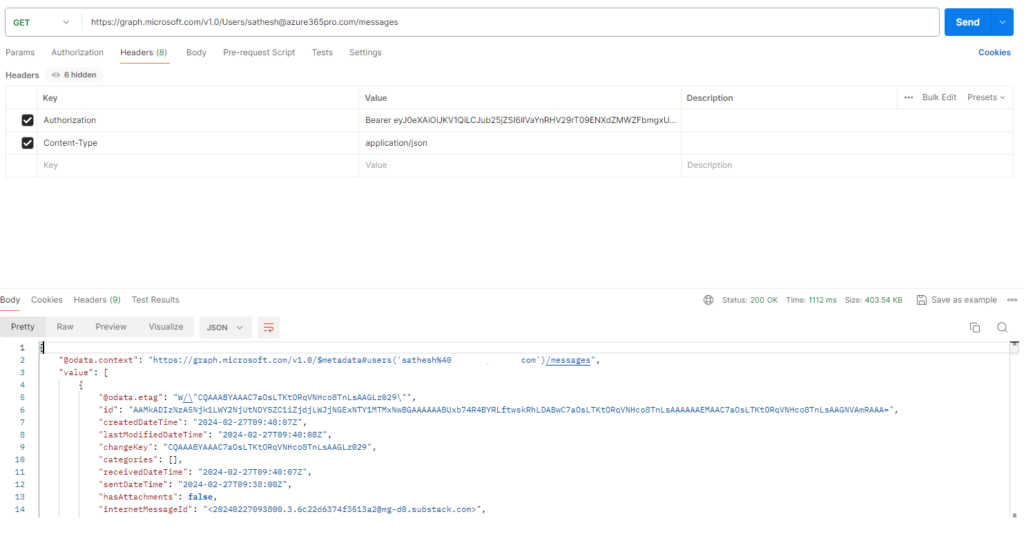
Trying to retrieve messages using the received token
https://graph.microsoft.com/v1.0/users/receiveattachments@localhost/messages
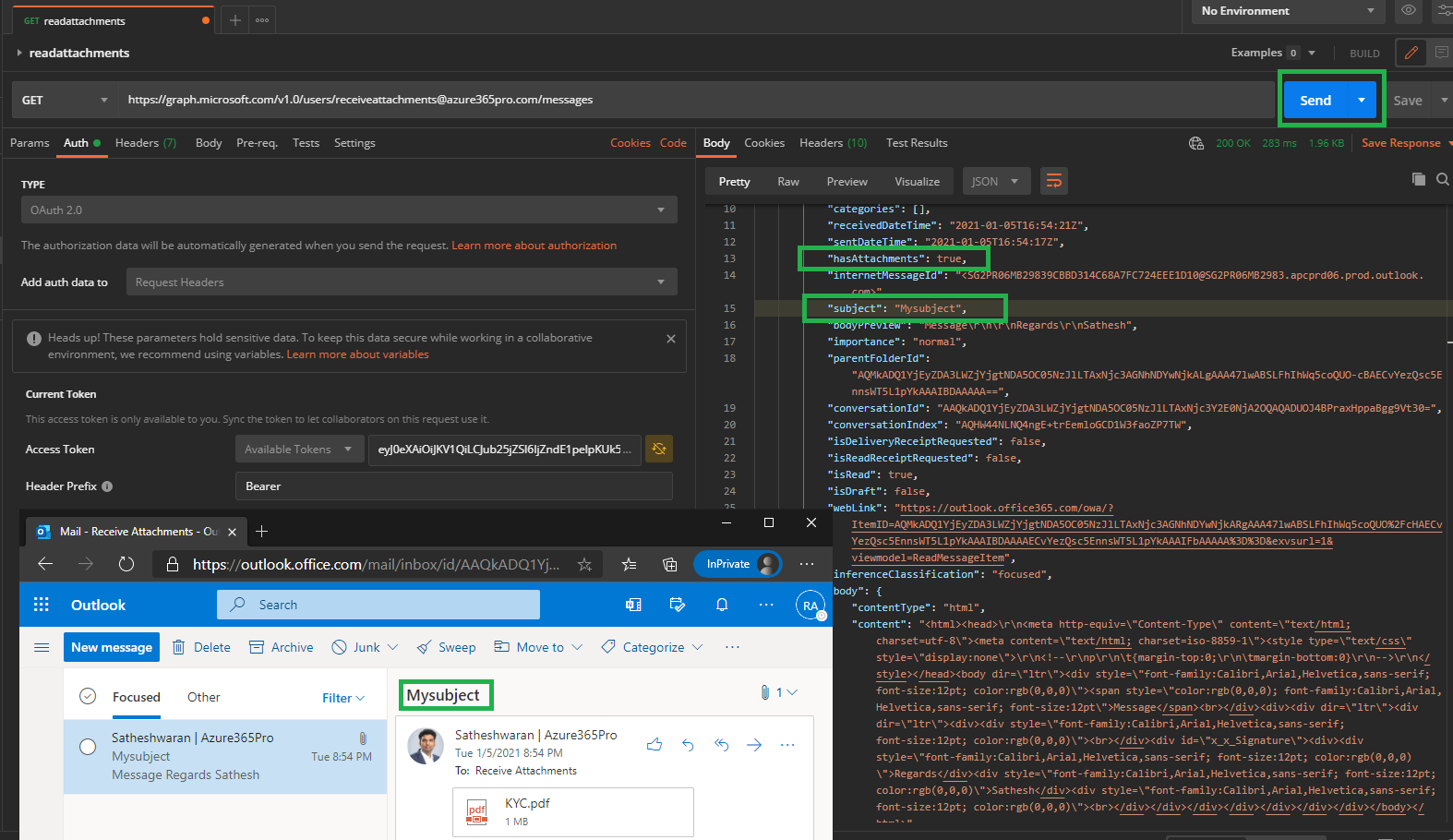
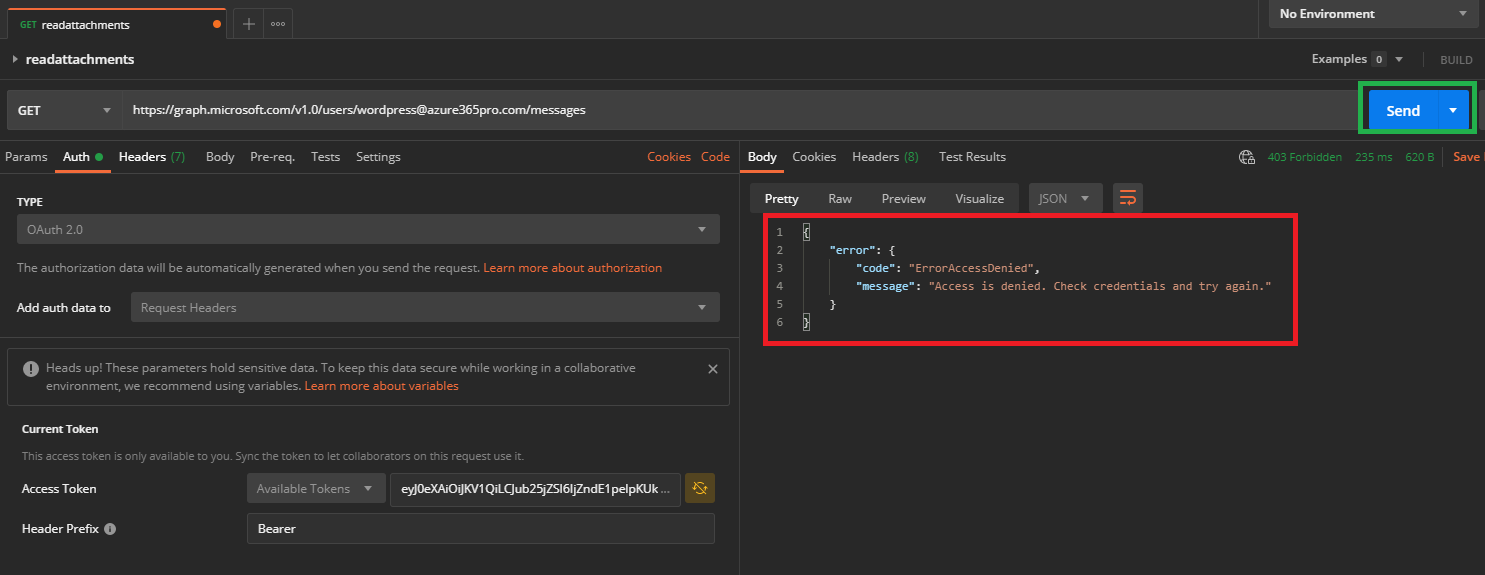
Trying to access the account that is not assigned to my enterprise application. where I can access messages from my service account only. Even after assigning the other account, I get the same error as expected. as the graph permission says to allow read-only for signed-in accounts only. As whichever account is used to receive the token it can retrieve messages from that account only.
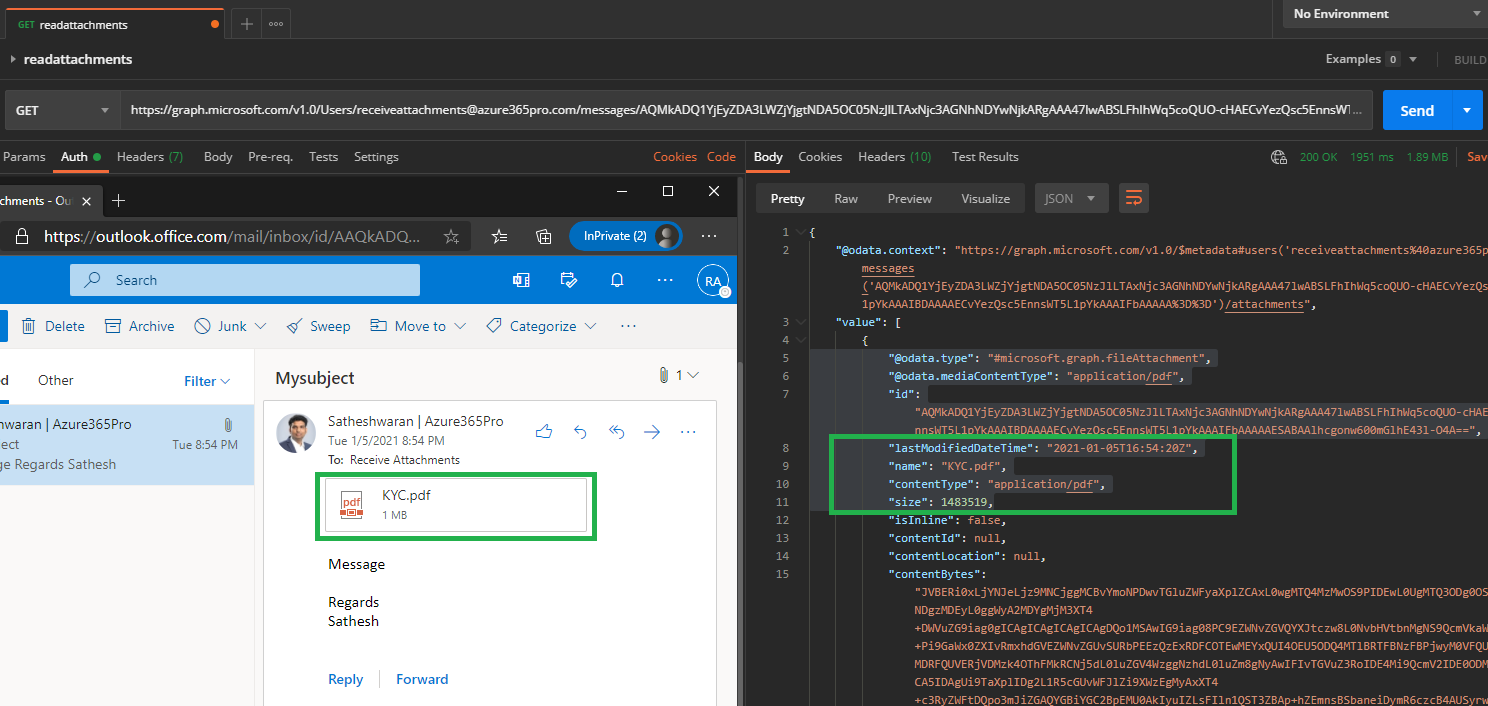
Let’s see how to retrieve the attachment using Microsoft Graph
Get the ID of the message to retrieve the attachment
https://graph.microsoft.com/v1.0/Users/receiveattachments@localhost/messages/AQMkADQ1YjEyZDA3LWZjYjgtNDA5OC05NzJlLTAxNjc3AGNhNDYwNjkARgAAA47lwABSLFhIhWq5coQUO-cHAECvYezQsc5EnnsWT5L1pYkAAAIBDAAAAECvYezQsc5EnnsWT5L1pYkAAAIFbAAAAA==/attachments
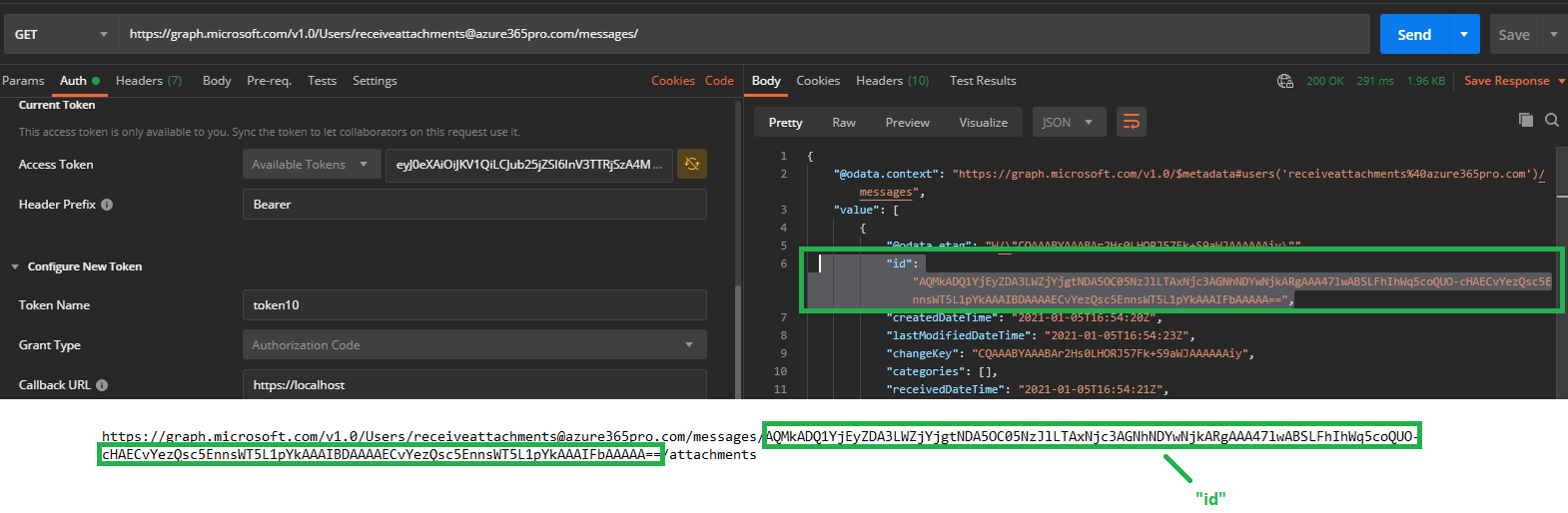
Now you can see the attachment is retrieved using Microsoft Graph.
Let’s consider you are developing a .NET console application and you want the application to retrieve the data without a signed-in user.
Then you need to Add Application permission for the application. So that they can retrieve without a sign-in prompt from the application. Now this application can read all the user mail from the environment. let’s see how to restrict them
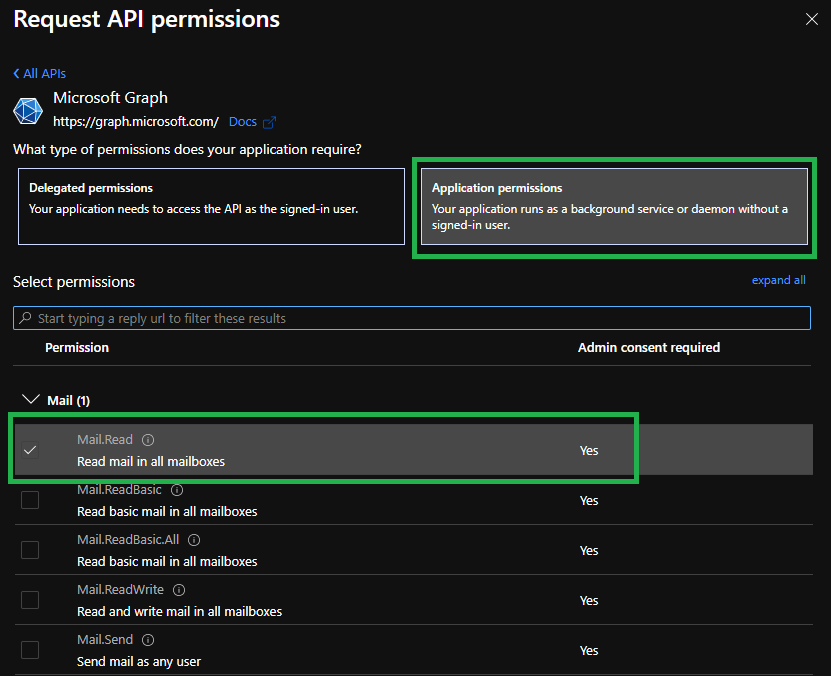
Mail.Read – Read mail in all mailboxes
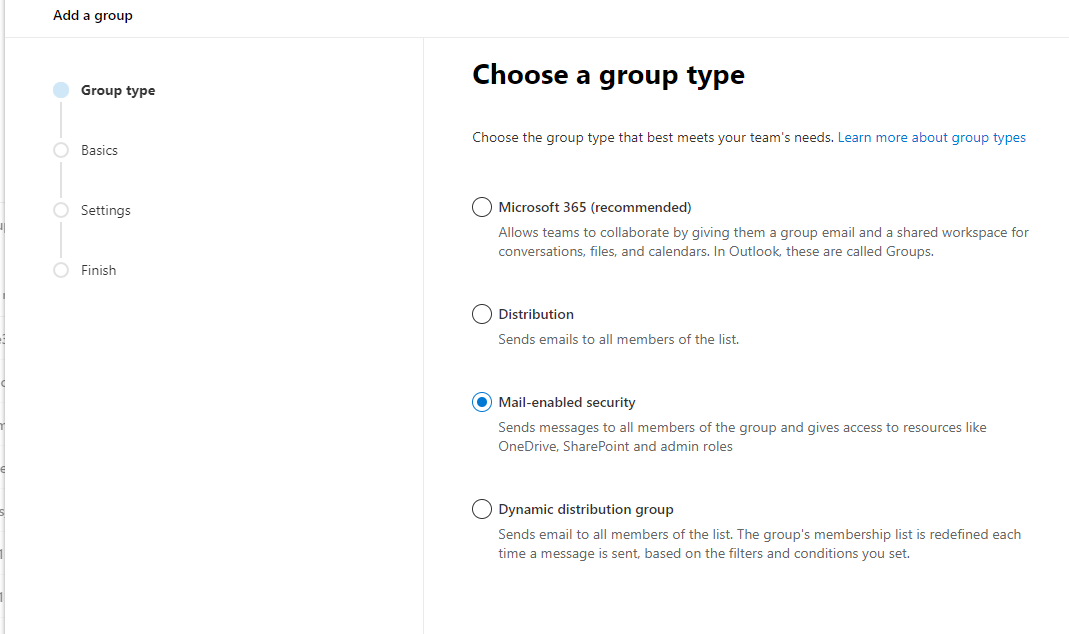
Create a Mail-Enabled Security group so that you can provide access only to the members of this group
New-ApplicationAccessPolicy -AppId 50f4b7ac-a83a-4f18-8b5a-81273f55a40d -PolicyScopeGroupId read.mail@localhost -AccessRight RestrictAccess -Description "Restrict this app to members of distribution group EvenUsers."
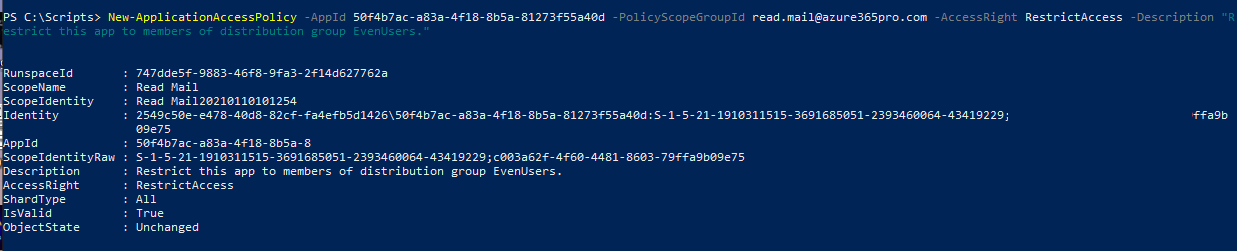
Client Credentials work if a user is a member of the mail security group we created. if a user is not a member we can Access denied.
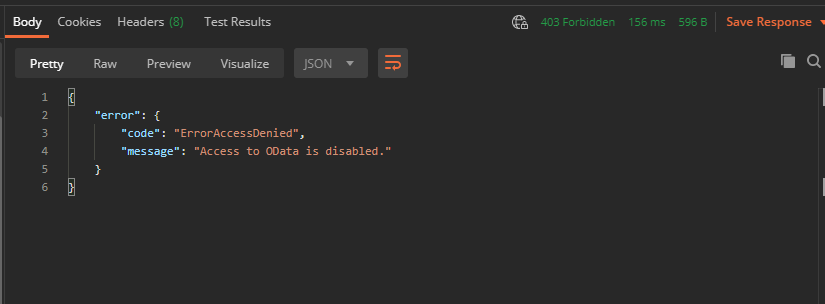
Error Access Denied “Access to OData is disabled” if the user is not a member of the mail security group
For Access Token and Retrieving Messages using Implicit Flow – Without Credentials
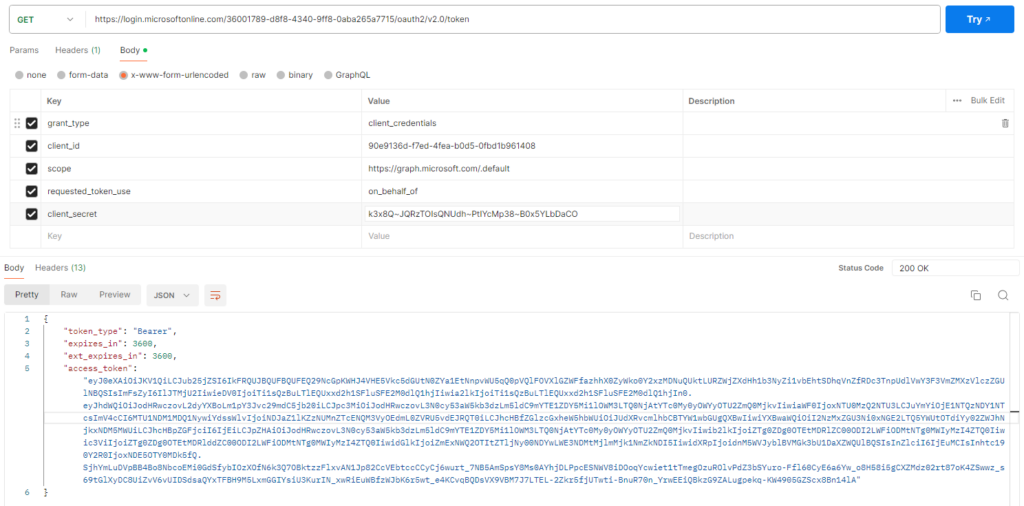
Now copy the access token without Quotes – Use it like
Authorization Bearer <AccessToken>

 \
\
Hi Satheshwaran –
thank you so much for the article on “Access Specific Office 365 Mailbox using Microsoft Graph” i have a question here, Microsoft is blocking Basic authentication in Exchange Online , it mean we can not connect to mailbox only with use id and password , in the given example connecting O365 mailbox with Graph API using delegated access permissions, mail box authentication using credentials are mandatory , it mean we are suing basic authentication again , is there any other option to use delegation permissions without using mailbox credentials?
thanks in advance !!!!