We will see below topics in this article
- Install Certificate Authority on Windows Server 2016
- Configuring Certificate Authority on Windows Server 2016
- Assigning Certificate on Exchange Server 2016
- Assigning on Test Machine to see Certificate authority is working for Outlook Web Access
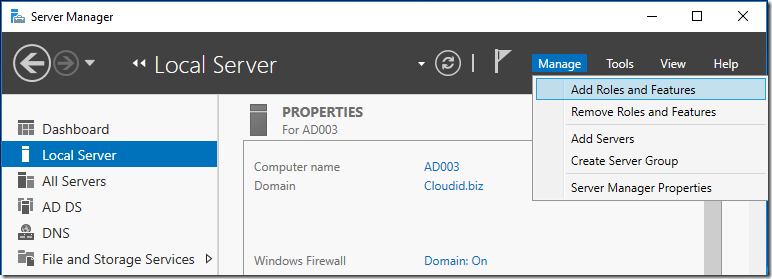
Step 1:
You need to have this role installed to have a Certificate Authority
Preferred to be on Dedicated Server or on a Domain Controller.
Open Server Manager – Manage – Add Roles and Features
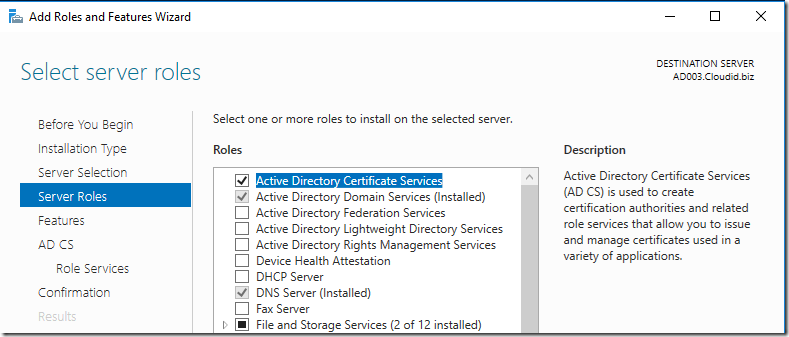
Step 2:
Choose : Active Directory Certificate Services
Choose Next
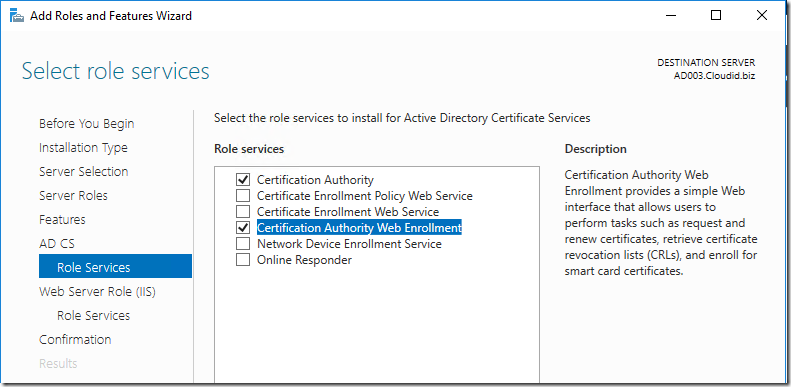
And Choose : Certification Authority Web Enrollment
Choose :
- Certification Authority
- Certification Authority Web Enrollment
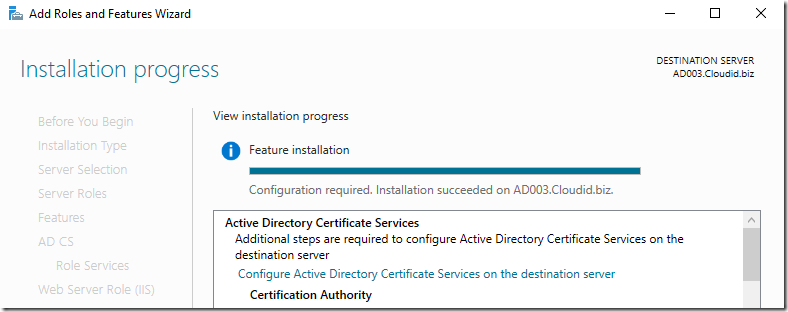
Choose Install and Close
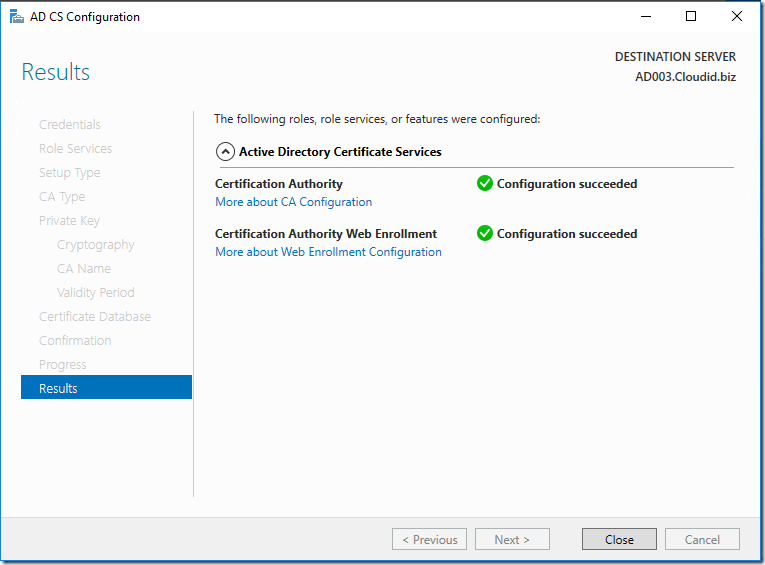
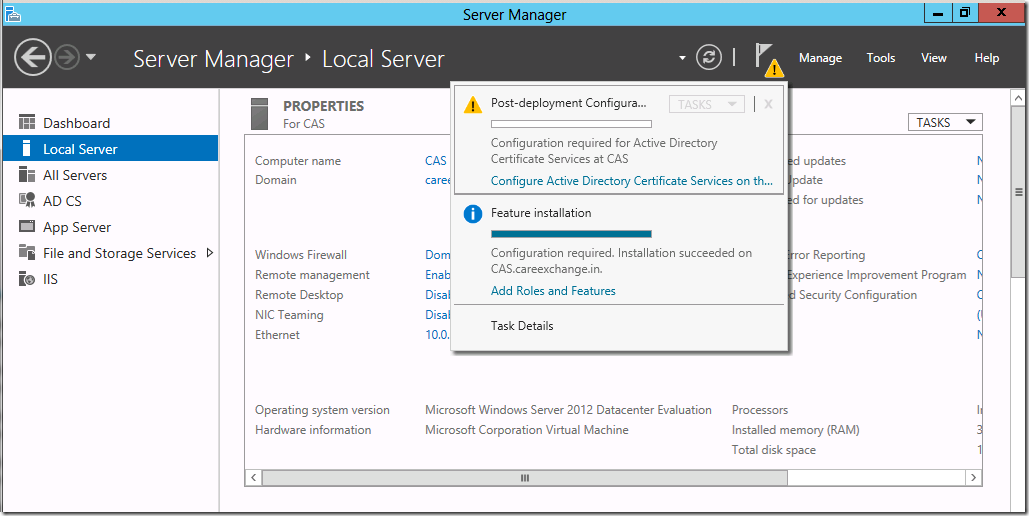
Step 3:
To Configure Active Directory Certificate Services – Choose the Exclamation Mark on the Flag
Configure Active Directory Certificate Services on the Destination Server
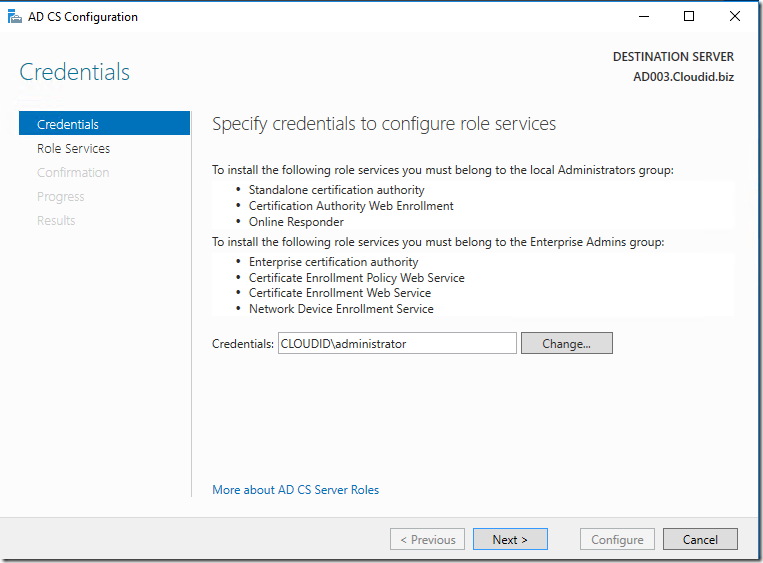
Choose Next
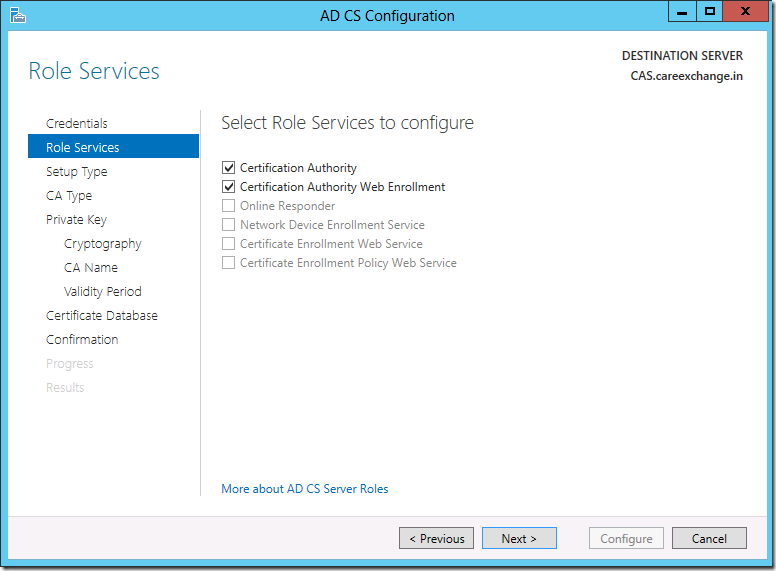
Choose
- Certificate Authority
- Certification Authority Web Enrollment
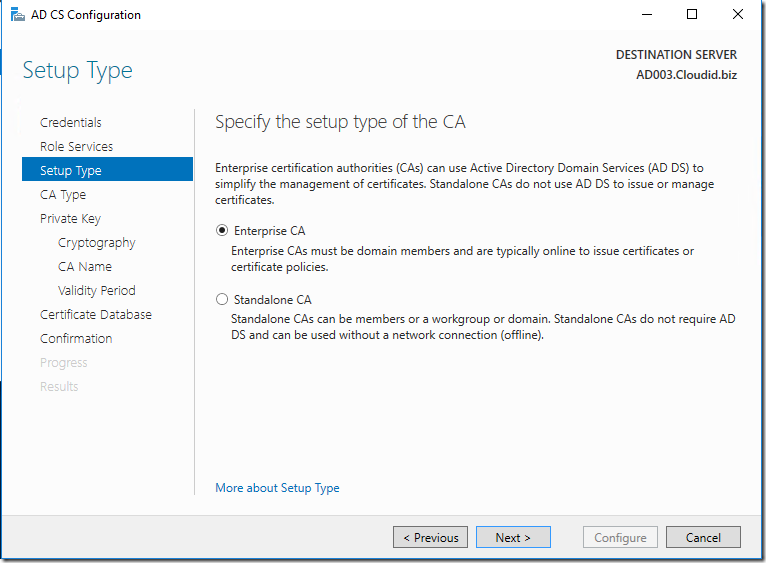
- Enterprise CAs Must be domain members and are typically online to issue certificates or certificate policies.
Step 4:
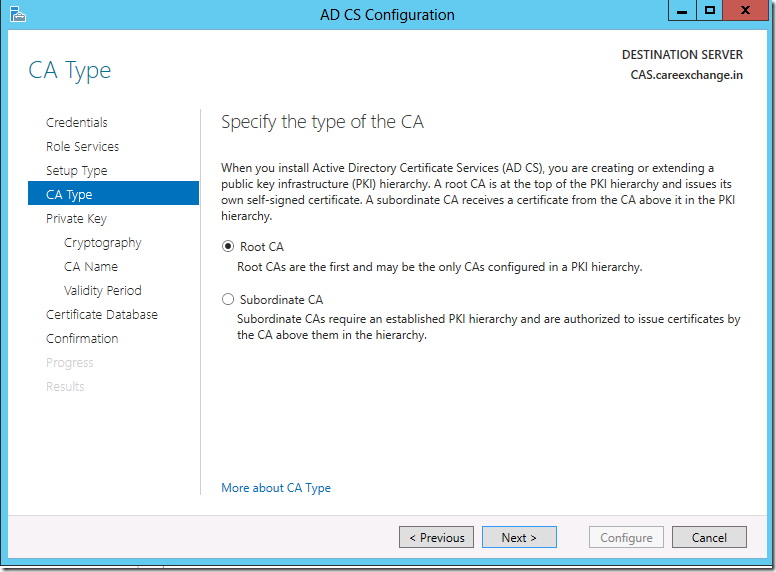
Choose Root CA
Root CAs are the first and may be the only CAs Configured in a PKI Hierarchy.
Step 5:
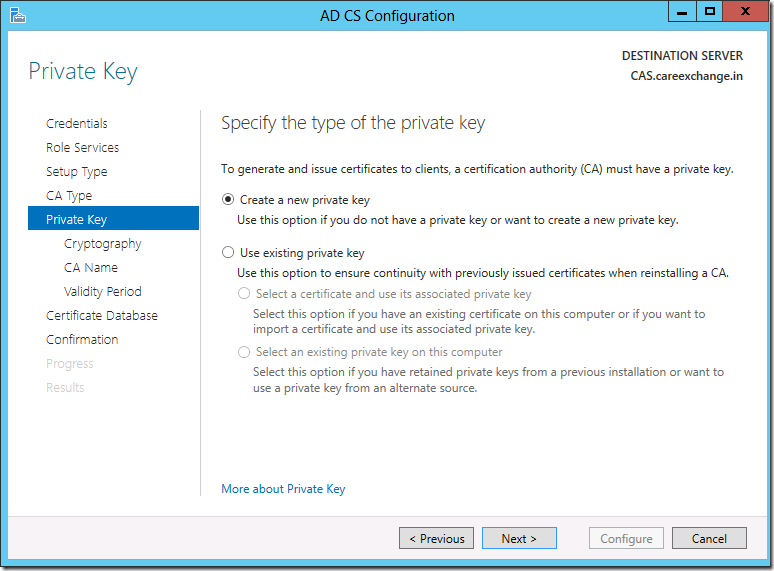
Create a new Private key
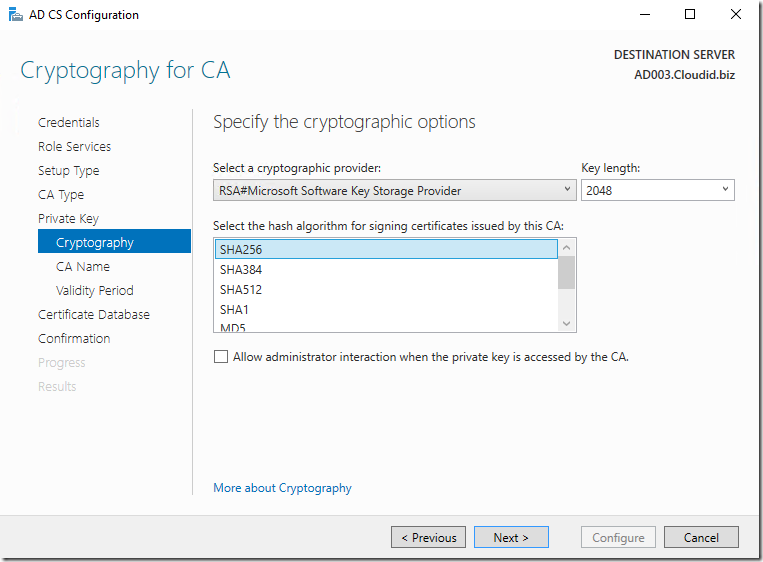
Step 6:
- Use SHA256
- RSA#Microsoft Software Key Storage Provider
- Key Length – 2048
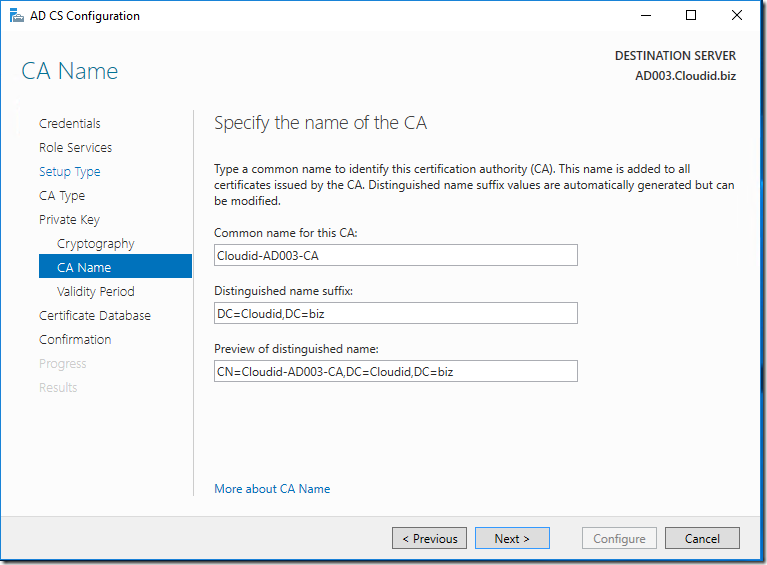
Step 7:
Click Next
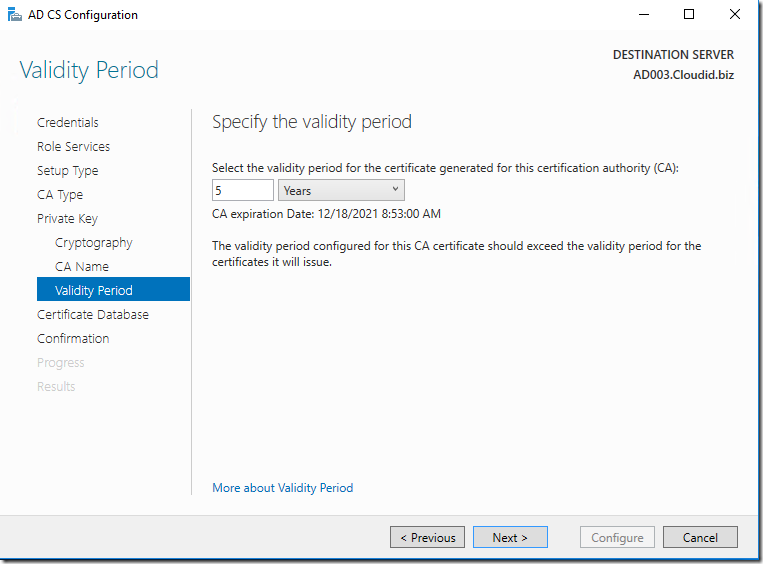
Step 8:
By Default Certificate is valid for 5 years , Don’t make any changes on it , Click next
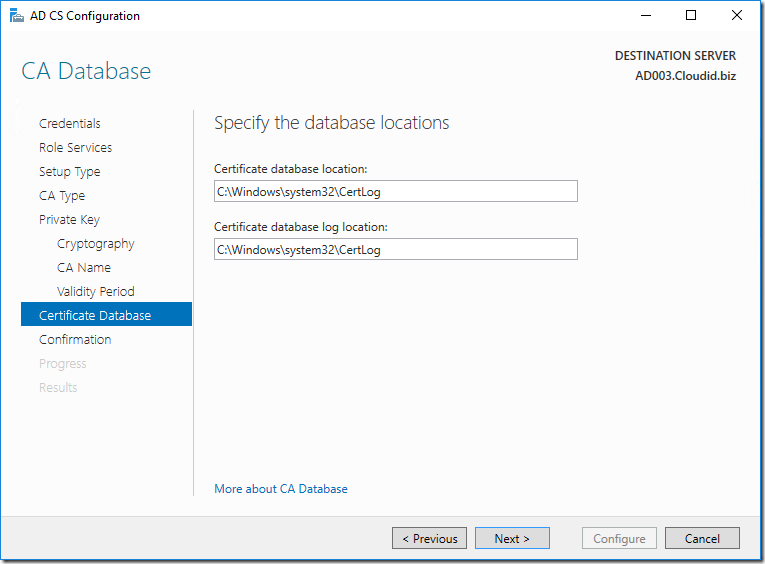
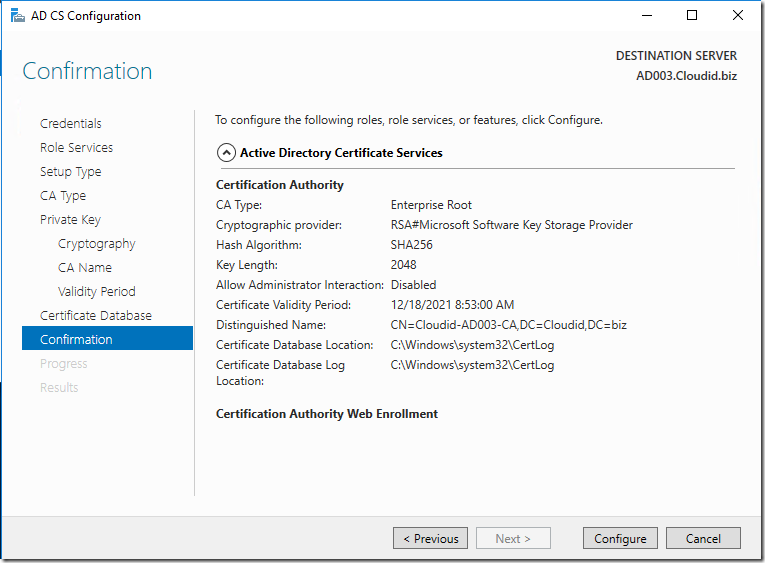
Step 9:
Specify Certificate Authority Default Database Locations
Click Configure
Choose Configure
We have successfully Installed and Configured – Certificate Authority on Windows Server 2016
Let us see how to Request a Create a Simple Cert from Internal Certificate Authority
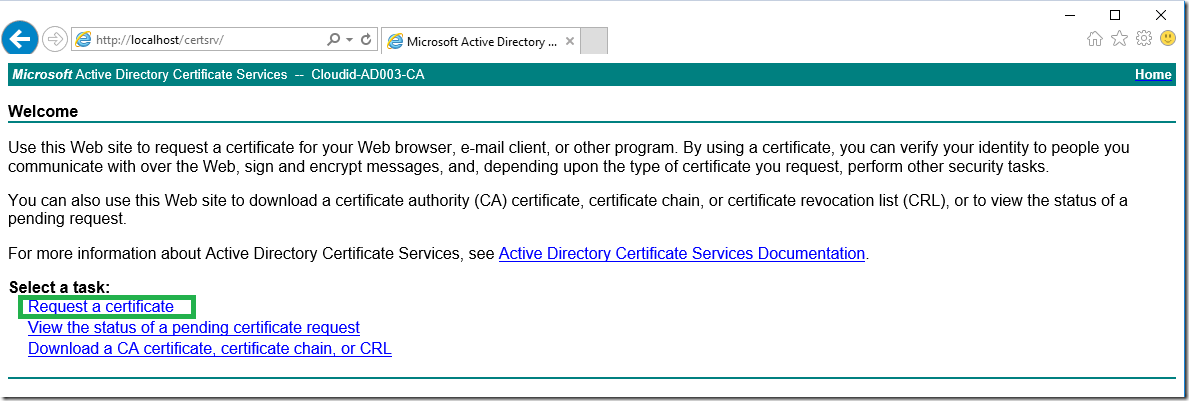
Step 10:
Browse http://localhost/certsrv/
You would see a page below like this , Choose “Request a Certificate”
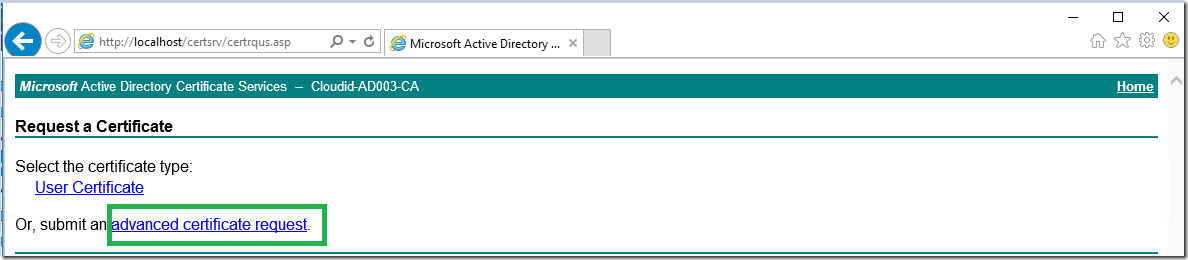
Step 11 –
Click on Advanced Certificate Request
Step 12:
Choose the Second one
Submit a certificate request by using a base-64-Encoded CMC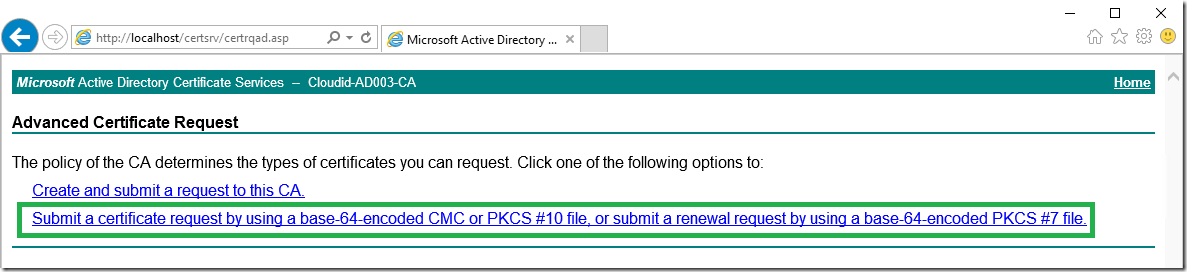
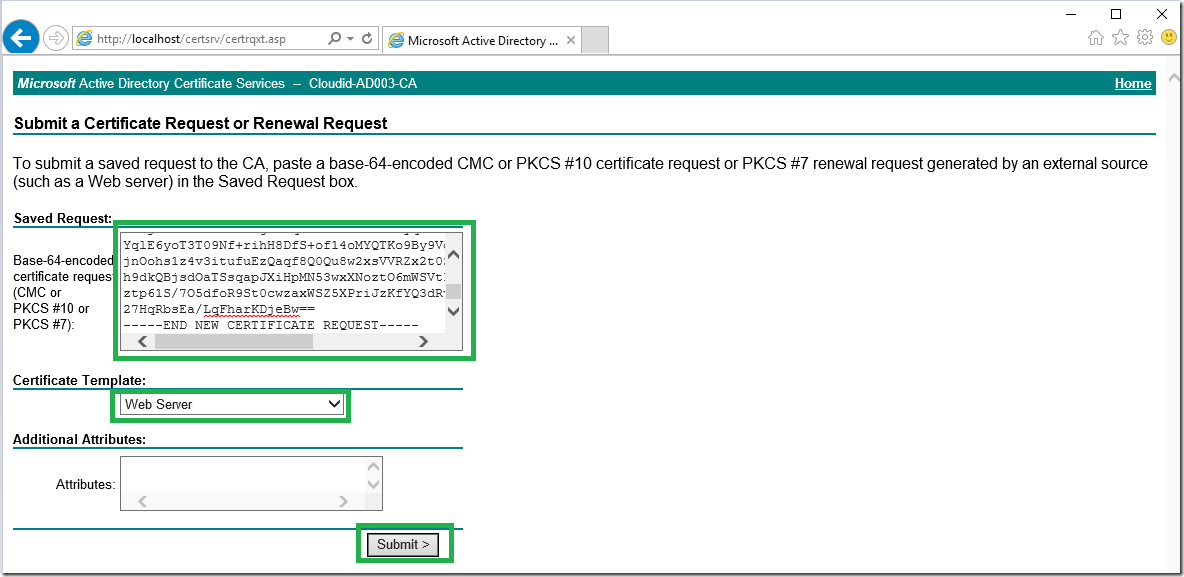
Step 13:
Now Copy the Note pad Certificate Request Data – You have to generate a Certificate Request from the application. For example how we are doing in exchange server
https://www.azure365pro.com/how-to-create-an-ssl-certificate-request-for-exchange-server-2013/
Or you can use https://www.digicert.com/util/
Example – Data Should be like below –
—–BEGIN NEW CERTIFICATE REQUEST—–
MIIEXDCCA0QCAQAwgYAxHTAbBgNVBAMMFGV4Y2gyMDE2LmNsb3VkaWQuYml6MRYw
FAYDVQQLDA1FeGNoYW5nZSBUZWFtMRUwEwYDVQQKDAxDYXJlRXhjaGFuZ2UxETAP
BgNVBAcMCE5ldyBZb3JrMRAwDgYDVQQIDAdOZXcgWW9yMQswCQYDVQQGEwJVUzCC
ASIwDQYJKoZIhvcNAQEBBQADggEPADCCAQoCggEBAKXVbwTkx4zhUobUvODoSwf1
8b0ti+dQ/WAoJPHlcSTW4weE5vVwQZbjtTqRhHOAOFEDYDnwZhuU1fOjjro+B2B3
zMTlvq0x7JJPsA9Zc611p+slYeTs/pI8hT9Ud2FgbwE3veF5u2uVw6/lbZdA20yU
ZizIsCJkq9Qo2hLpMji3MB4eFRtyvd1eQpCJPnqseUdRVzfdSwN2zf0U7UQCzzG+
q7bL1Pb2jfjFlhr5xb9/RfpaR/U3TmVHjf3/u49mK1JOBuJwJQVCK/HBYHfMPOp6
VEjt8IVApclOE7tZcR3DjjyF73tHYfxUJp2HuVWml/UVemKIcSfVYOcGofNrF88C
AwEAAaCCAZQwGgYKKwYBBAGCNw0CAzEMFgo2LjIuOTIwMC4yMF8GCSsGAQQBgjcV
FDFSMFACAQUMFEVYQ0gyMDE2LkNsb3VkaWQuYml6DBFDTE9VRElEXEVYQ0gyMDE2
JAwiTWljcm9zb2Z0LkV4Y2hhbmdlLlNlcnZpY2VIb3N0LmV4ZTByBgorBgEEAYI3
DQICMWQwYgIBAR5aAE0AaQBjAHIAbwBzAG8AZgB0ACAAUgBTAEEAIABTAEMAaABh
AG4AbgBlAGwAIABDAHIAeQBwAHQAbwBnAHIAYQBwAGgAaQBjACAAUAByAG8AdgBp
AGQAZQByAwEAMIGgBgkqhkiG9w0BCQ4xgZIwgY8wDgYDVR0PAQH/BAQDAgWgMFAG
A1UdEQRJMEeCFGV4Y2gyMDE2LmNsb3VkaWQuYml6ghhBdXRvRGlzY292ZXIuQ2xv
dWRpZC5iaXqCCEVYQ0gyMDE2ggtDbG91ZGlkLmJpejAMBgNVHRMBAf8EAjAAMB0G
A1UdDgQWBBQWEHXi+M7zoQZ3FlnOeRqsRscG0jANBgkqhkiG9w0BAQUFAAOCAQEA
FlYjkXO1rxadJmNB9g9KEqWU7NlxC3UdX2zyqWwK06cDB3/k+ThKBiYE7uoiaais
YqlE6yoT3T09Nf+rihH8DfS+of14oMYQTKo9By9VdisD6R/iztY05StbVoSambRk
jnOohs1z4v3itufuEzQaqf8Q0Qu8w2xsVVRZx2t0SKfktPASqOzJZEIRS6egqELH
h9dkQBjsdOaTSsqapJXiHpMN53wxXNoztO6mWSVtPzgbfML0+NLT41ZBiIAMjyIj
ztp61S/7O5dfoR9St0cwzaxWSZ5XPriJzKfYQ3dRvl+j/e1gi/rJmw9IUyWGQ2qz
27HqRbsEa/LqFharKDjeBw==
—–END NEW CERTIFICATE REQUEST—–
SavedReqest – (NEW CERTIFICATE REQUEST Data like above)
Choose Template : WebServer
Choose Submit
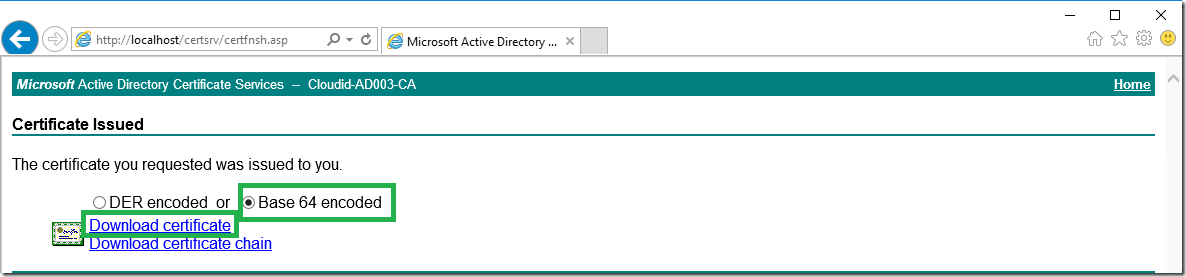
Step 14:
Choose “Base 64 encoded”
Download Certificate
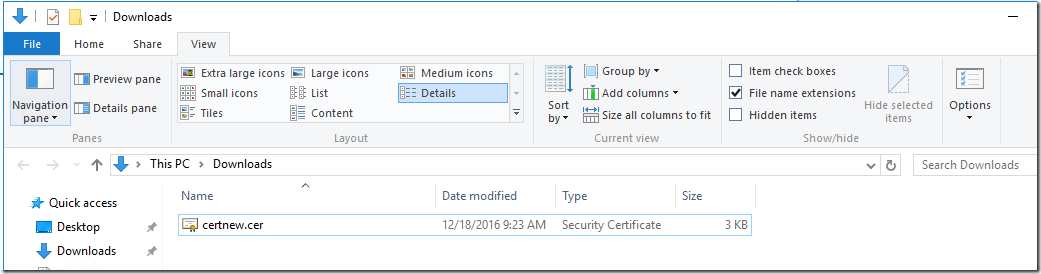
Step 15:
Save the Certificate – should be .cer extension
–
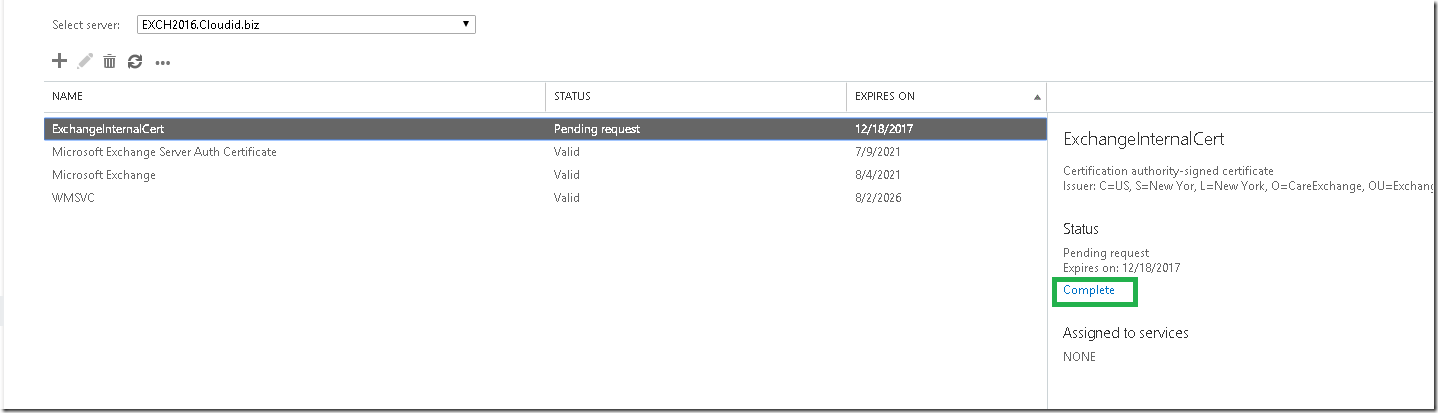
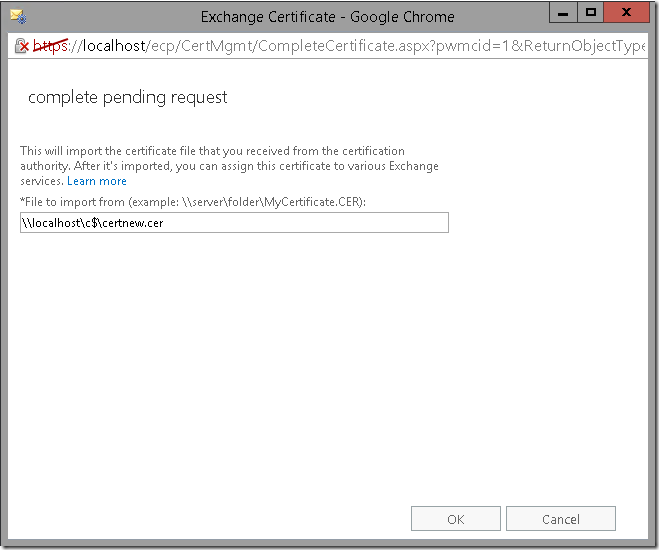
Lets how we are applying on Exchange 2016 for Example
Copied my Request .CER File generated from CA to the Exchange and using it.
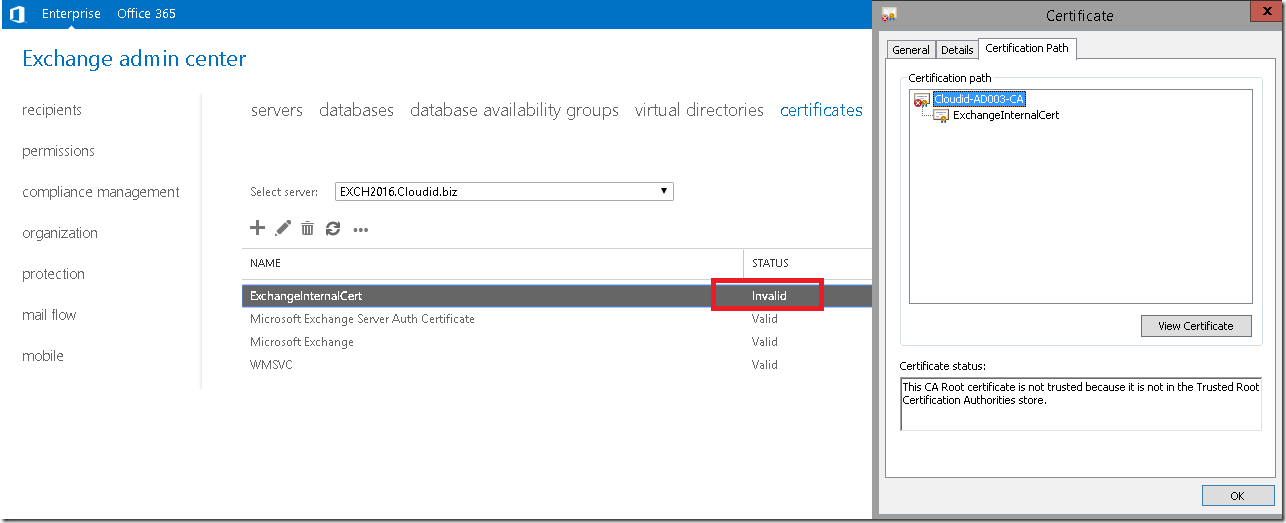
Shows Certificate Invalid.
Lets see why.
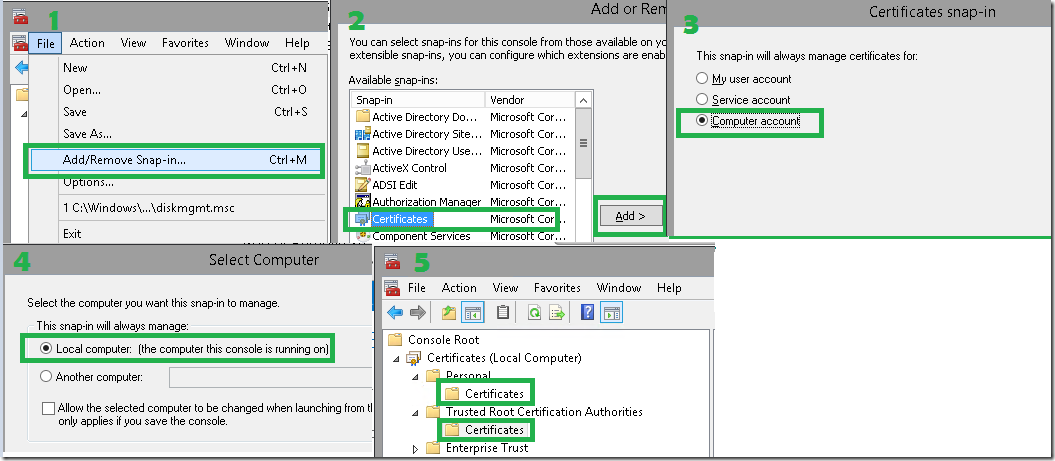
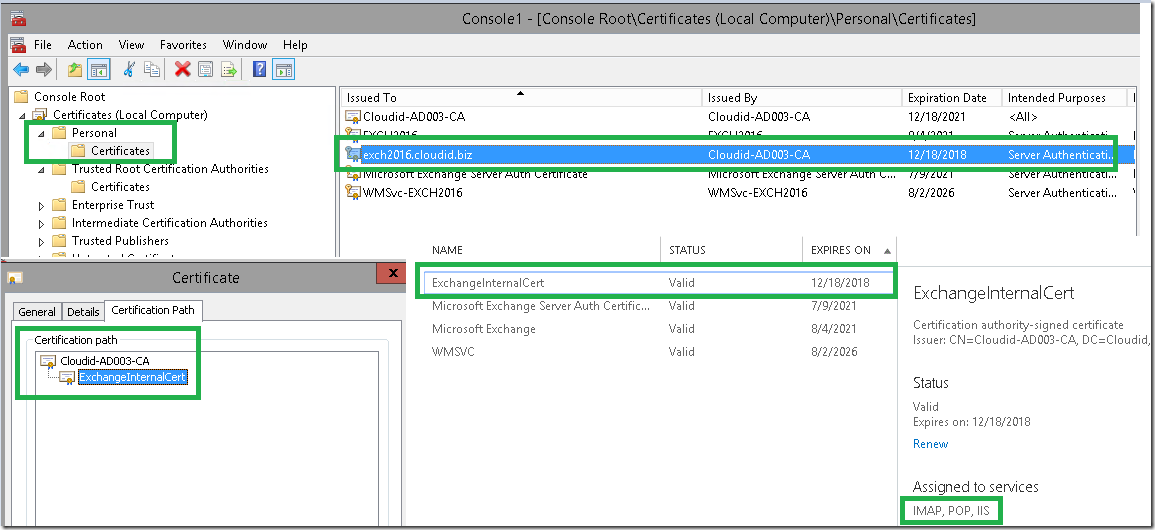
1 – Start – MMC –FILE – Add/Remove Snap-In
2 – choose certificates – Add
3 – Computer Account
4 – Local Computer
5 – Expand Personal – Certificates / Expand Trusted Root Authorities Certificates
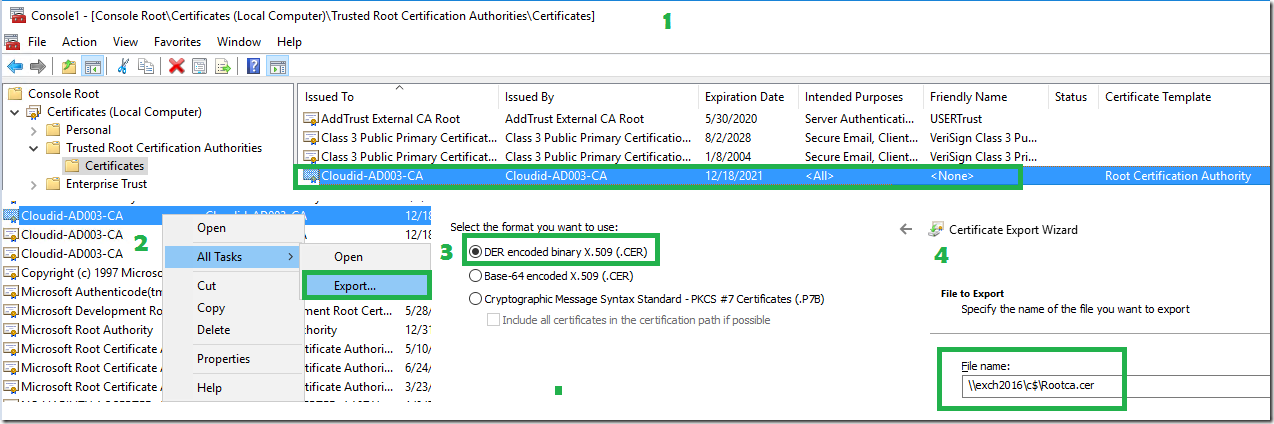
Now Login to Root CA Server and Export the Root CA.
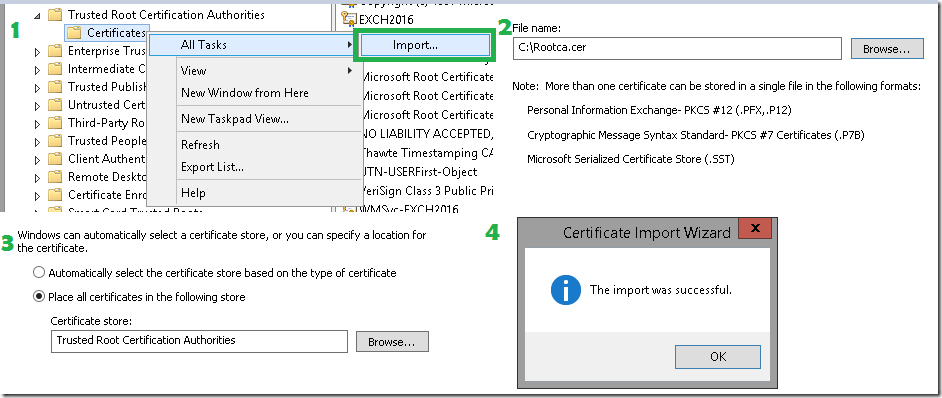
Now login to Exchange Server Import the export cert.
Now Certificates looking ok
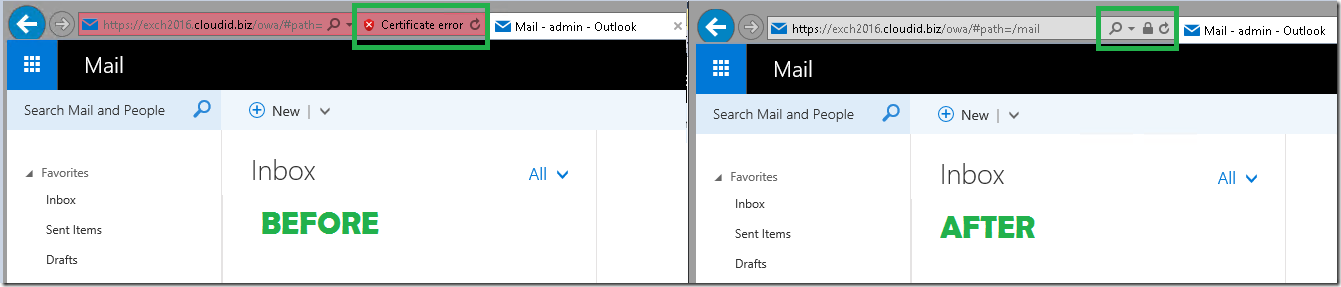
Make sure you Assign the Certificate for IIS in Exchange Control Panel.
Now you can see things are fine locally on Exchange 2016 server –
– Lets see how we can use on Desktop
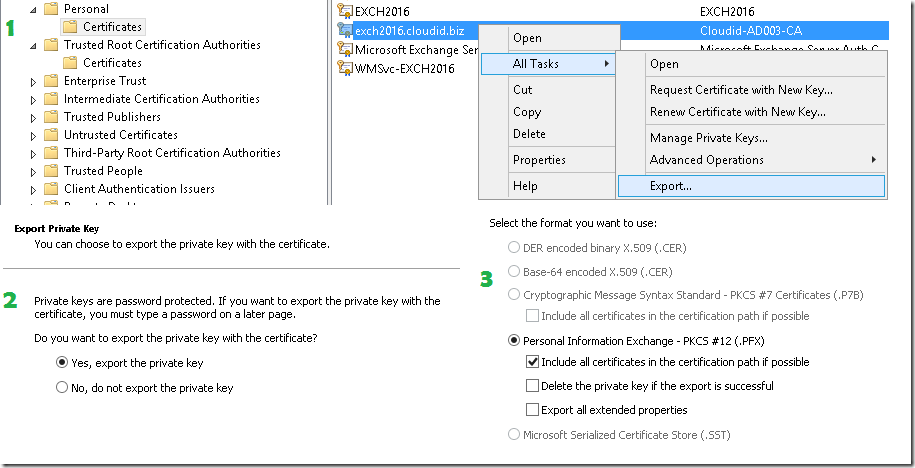
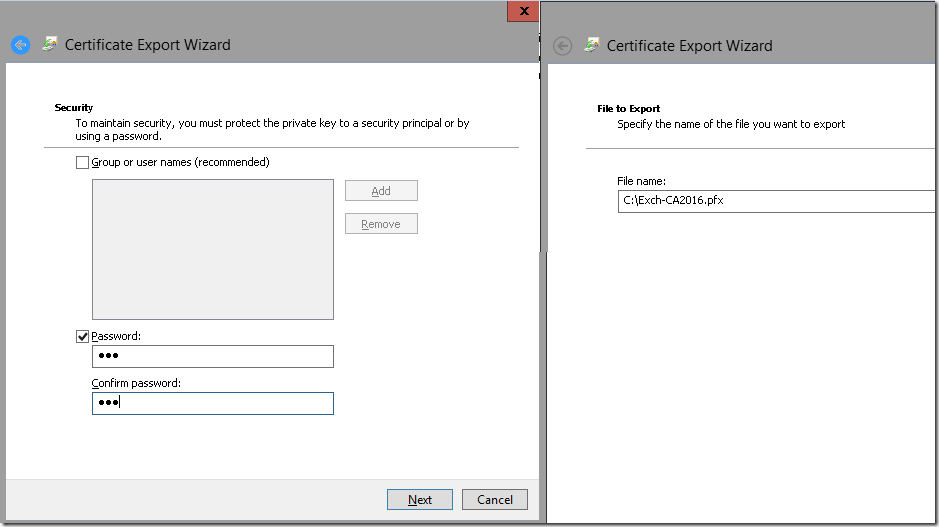
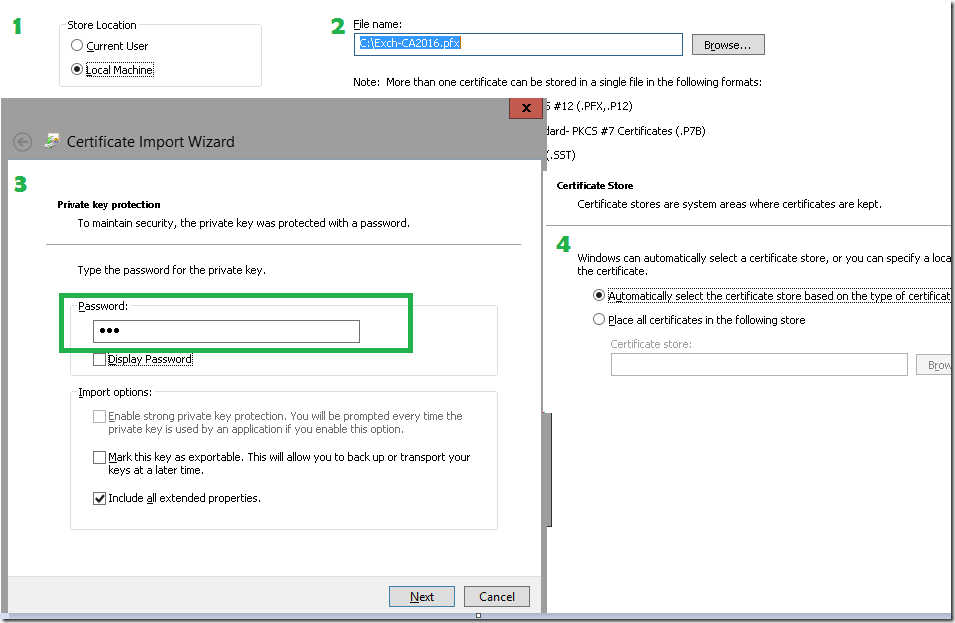
First Login to Exchange Server MMC and Export the Certificate with all the certificate path into a PFX file.
Note : The desktop doesn’t need the private keys from any certificate in the chain.
Having the private key gives the ability to decrypt all the traffic between the client and the server even if that traffic is coming from someone else. It also makes a man in the middle attack on this SSL connection possible.
On 2 : For End user desktops – Choose do no export private key and use that certificate for import.
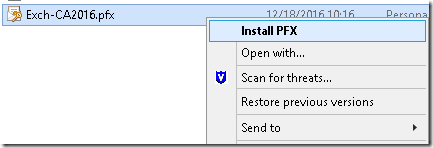
Now we have the PFX File Exported.
Open MMC and Import or Install PFX Desktop.
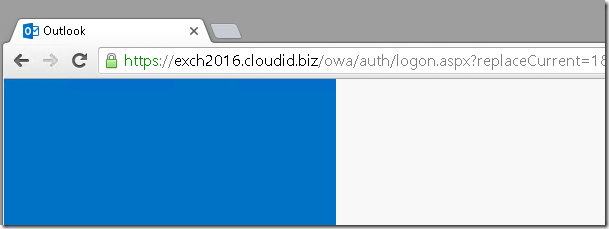
Now browsing the URL –


You make one big mistake in this tutorial, you’re exporting the private key to the desktop. As the name “private” key says, you should never export this one outside of the server that uses the certificate and keep it private. Only export the public keys to deploy them on the desktop’s. The desktop doesn’t need the private keys from any certificate in the chain.
Having the private key gives the ability to decrypt all the traffic between the client and the server even if that traffic is coming from someone else. It also makes a man in the middle attack on this SSL connection possible.
Updated the Post. Thank you for your feedback Wouter. You are right.
Updated the text of the post, but your examples screenshots are still wrong in that area. Just for clarification
I read the comments and while they are valid, I personally appreciate the fact that someone has taken the time out and out in some effort to produce this document.
This gives users who are not aware of the technology some perspective on its purpose.
Great Tutorial. Keep up the good work
I would like to know if this needs be configured in a standalone server, or it needs to be in the domain controller for example. Or it need to have any additional roles like DNS.
Thanks and best Regards
Reply to JP:
If you need the cert server to be online to issue certificate, it should be installed server which is a member of the domain. This does not have to be a DC.
Sorry to be pickt, but you should never ever have you Root CA online and within your CA!
The Root CA should always be offline and not in the domain.
This would be the Job of an intermediate or issue CA.
Can you please clarify why?
This is correct. The root CA is created to produce the private key, then removed and kept safe. The domain/chain does the rest of the work.